TL;DR:
- Choosing the right smart security solution depends on sector-specific needs, compliance, and scalability.
- AI-driven threat detection enhances security responsiveness and reduces false alarms across industries.
- Integrated cloud platforms provide centralized control and scalability for organizations managing multiple sites.
Selecting the right smart security solution is one of the most consequential decisions an IT or security leader can make. Get it right and you strengthen safety, satisfy auditors, and improve operational efficiency across your organisation. Get it wrong and you face compliance gaps, integration headaches, and systems that staff simply do not use. For organisations in education, manufacturing, and hospitality, the stakes are particularly high — each sector carries distinct regulatory demands, asset profiles, and user populations. This article walks through the key evaluation criteria, leading solution types, and sector-specific recommendations to help you make a confident, informed choice.
Table of Contents
- Criteria for evaluating smart security solutions
- Access control and surveillance: pillars of smart security
- AI-driven threat detection and response systems
- Cloud-based and integrated security platforms
- Choosing the right solution for your sector
- A smarter path: lessons from real implementations
- Upgrade your security strategy with expert guidance
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Define your criteria | Start by clarifying your regulatory, operational, and sector priorities before comparing solutions. |
| Leverage AI and integration | AI and unified platforms multiply detection speed and management efficiency. |
| Match solutions to sector needs | Optimal security depends on aligning technology strengths with unique risks in your sector. |
| Plan for adaptability | Choose solutions flexible enough to evolve with compliance and operational changes. |
Criteria for evaluating smart security solutions
Before comparing products or vendors, it pays to establish clear evaluation criteria. Smart security must balance compliance and operational continuity, which means your assessment framework needs to reflect both dimensions from the outset.
Here are the core criteria every IT decision-maker should apply:
- Regulatory compliance: Education institutions must address safeguarding obligations and data protection law. Manufacturers face ISO standards and health-and-safety mandates. Hospitality operators must manage guest privacy under GDPR. Each context demands sector-appropriate compliance tooling.
- Core capabilities: Look for real-time monitoring, remote control, scalability across sites, and the ability to integrate with existing infrastructure. A solution that cannot scale with your organisation creates technical debt quickly.
- Ease of deployment and management: Complex rollouts increase the risk of misconfiguration. Prefer solutions with clear management interfaces, documented APIs, and active vendor support.
- Total cost of ownership: Upfront licence fees are rarely the full picture. Factor in ongoing support, hardware refresh cycles, training costs, and the cost of downtime during deployment.
- Sector-specific requirements: Universities need to protect student data and manage high volumes of visitors. Manufacturers must safeguard intellectual property and production environments. Hospitality venues need granular visitor management and real-time responsiveness.
Pro Tip: Prioritise solutions with modular features. A modular architecture allows you to activate only what you need now, then expand capabilities as sector requirements evolve, without replacing the underlying platform.
Evaluating security for diverse industries through this structured lens prevents the common mistake of buying technology that is impressive in a demo but misaligned with your operational reality.
Access control and surveillance: pillars of smart security
Access control and surveillance form the physical foundation of any smart security strategy. Surveillance and access control improve both preventive and responsive security, giving organisations the ability to deter threats before they escalate and investigate incidents thoroughly when they do occur.
The most common system types include:
- Biometric authentication: Fingerprint or facial recognition provides high-assurance access control. Well suited to research labs, server rooms, and manufacturing clean zones where tailgating is a serious risk.
- Card and fob entry: A practical, cost-effective choice for high-throughput environments. Easily managed centrally and revoked instantly. Common in hotel corridors and multi-building campuses.
- IP surveillance cameras: Network-connected cameras enable remote monitoring, cloud storage, and integration with AI analytics. Essential for large sites with limited on-site security staff.
| System type | Strengths | Sector fit | Relative cost |
|---|---|---|---|
| Biometric authentication | High assurance, non-transferable | Manufacturing, higher education | High |
| Card/fob entry | Scalable, easy revocation | Hospitality, education | Low to medium |
| IP surveillance | Remote access, AI-ready | All sectors | Medium |
| Video analytics | Automated alerts, pattern detection | Manufacturing, hospitality | Medium to high |
In practice, a university might use card entry for general buildings while applying biometric controls in sensitive research facilities. A hotel chain may deploy IP cameras in public areas and card systems for staff-only corridors. Manufacturers often combine all three layers, particularly when protecting high-value equipment or proprietary processes.
The forensic value of smart building security should not be underestimated either. Time-stamped access logs and video evidence are increasingly required by insurers and regulators alike.

AI-driven threat detection and response systems
Physical boundaries alone are no longer sufficient. Modern smart security relies on artificial intelligence to detect threats that human operators or rule-based systems would miss. AI enables advanced threat detection and automation, enabling organisations to respond faster and with greater precision than traditional approaches allow.
Key AI-driven capabilities to look for include:
- Behavioural analysis: Cameras and network sensors learn what is normal for your environment and flag deviations. A person loitering near a restricted area or an unusual spike in data transfers can both trigger automated alerts.
- Smart alerting: Rather than generating thousands of low-quality notifications, modern AI-based systems filter events by severity and context, reducing alert fatigue for security teams.
- Automated lockdowns: In manufacturing, if an intrusion is detected on the production floor outside shift hours, an AI-integrated system can automatically lock access points and notify response teams without human intervention.
- Network anomaly detection: Universities with large, open networks face significant insider threat risks. AI-driven tools continuously analyse traffic patterns and isolate suspicious behaviour in near real time. Good digital security essentials practices combine network and physical monitoring for maximum coverage.
For hospitality operators, real-time guest threat alerts — triggered by crowd analysis or unusual activity near cashpoints and reception areas — improve both guest safety and staff response times.
Pro Tip: Continuously train AI models on sector-specific data. A model trained on generic datasets will generate more false positives in your environment. Work with your vendor to feed it real operational data from your sites during onboarding and at regular intervals thereafter.
The benefits are clear: faster detection, fewer disruptions caused by false alarms, and adaptable algorithms that improve over time when properly maintained.
Cloud-based and integrated security platforms
Individual tools are valuable, but organisations managing multiple sites or complex user populations gain the most from integrated platforms. Cloud integration streamlines deployment and monitoring for distributed sites, providing centralised visibility and control that standalone systems simply cannot match.
| Platform feature | Benefit | Example use case |
|---|---|---|
| Unified dashboard | Single pane of glass management | University with multiple campuses |
| API integration support | Connects with SIEM, HR, and access tools | Manufacturing with existing ERP |
| Centralised audit logs | Simplifies compliance reporting | Hotel chain under GDPR audit |
| Cloud-native scalability | Adds sites without hardware overhead | Growing hospitality group |
For decision-makers considering a cloud-first approach to cloud security strategies, the transition typically follows four steps:
- Audit your current environment: Catalogue existing hardware, software, access rights, and integration points. Identify gaps and legacy risks.
- Plan the migration: Define a phased roadmap that avoids operational disruption. Prioritise high-risk areas first.
- Train your team: Even the best platform fails if staff do not understand how to use it. Invest in role-specific training before go-live.
- Roll out and iterate: Deploy in stages, monitor performance, and adjust policies based on real-world feedback.
The cloud network advantages are particularly compelling for organisations with distributed footprints, such as multi-academy trusts, branded hotel chains, or manufacturers with several production sites. Centralised policy control means a change made at head office propagates instantly across every connected location.
Choosing the right solution for your sector
With all the options reviewed, the final step is matching solution types to sector priorities. This is where many organisations lose focus by selecting best-in-class tools that do not fit their specific context.
| Sector | Priority focus | Recommended solution types |
|---|---|---|
| Education | Safeguarding, visitor management, data protection | Card/biometric access, IP surveillance, cloud platform |
| Manufacturing | Asset protection, perimeter security, IP safeguarding | Biometric access, AI analytics, layered network security |
| Hospitality | Guest privacy, real-time alerting, compliance | IP cameras, video analytics, integrated cloud platform |
“Organisations that adopt a layered security for manufacturers approach — combining physical, digital, and cloud-based controls — consistently outperform those relying on single-layer solutions in both incident response times and compliance outcomes.”
For education, safeguarding students and managing a fluid population of pupils, staff, and visitors demands a combination of reliable physical access controls and cloud-based logging. Privacy compliance is non-negotiable.
Manufacturers benefit most from a layered approach that protects both the physical environment and the IP held on internal networks. Perimeter control, combined with AI-driven anomaly detection, delivers the depth of defence that sector demands.
Hospitality organisations must balance guest experience with safety. Solutions that operate quietly in the background, triggering alerts only when genuinely needed, are far preferable to intrusive setups that undermine guest comfort.
The next step for any organisation is an honest internal audit, followed by a structured vendor assessment against the criteria outlined here.
A smarter path: lessons from real implementations
After working across education, manufacturing, and hospitality deployments, one truth stands out consistently: the organisations that struggle most are not those that chose the wrong technology. They are the ones that chose the right technology and then underinvested in implementation, training, and ongoing governance.
“Smart” is a label applied generously by vendors. In practice, a system is only as intelligent as the data it receives and the processes built around it. We have seen AI-powered platforms generate more noise than insight because no one configured the baseline thresholds for that specific site. We have seen biometric systems bypassed by simple workarounds because user training was skipped to meet a deployment deadline.
The most overlooked issue in security purchasing is long-term adaptability. Sector requirements change. Regulations evolve. Staff turnover shifts your risk profile. The organisations that maintain strong security posture over time are those that treat their security platform as a living system, not a one-time purchase. Build in regular reviews, budget for reconfiguration, and maintain a relationship with your technology partner that goes beyond the initial sale.
Upgrade your security strategy with expert guidance
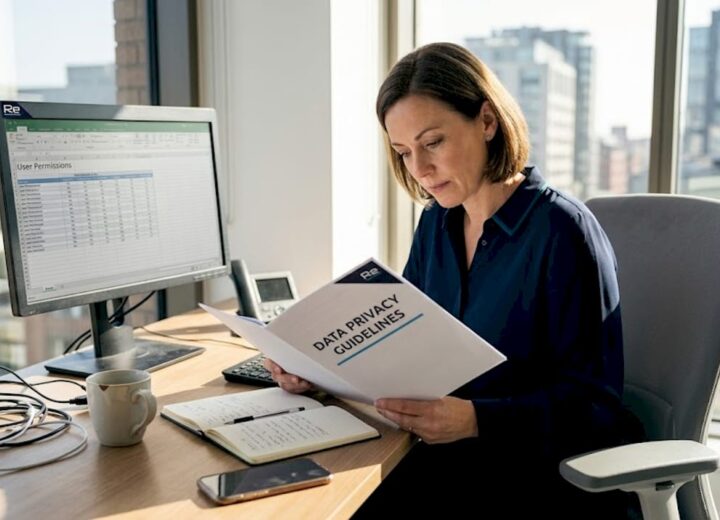
If you are ready to move beyond a reactive security posture, the right expertise can make the difference between a deployment that works and one that merely exists. Re-Solution brings over 35 years of experience helping organisations in education, manufacturing, and hospitality design, deploy, and optimise smart security solutions aligned to their specific sector needs.
Whether you need help assessing your current infrastructure, exploring network as a service options, or understanding what IT infrastructure explained means for your security architecture, our technical specialists are ready to help. There is no obligation and no generic pitch — just a focused conversation about your environment and your goals. Speak to our team today and take the next step towards a security strategy built for your sector.
Frequently asked questions
What is a smart security solution?
A smart security solution integrates advanced technology such as AI, IoT, or cloud to automate, monitor, and enhance physical or digital security operations. Smart building technologies that combine these layers deliver both efficiency and stronger safety outcomes.
Are AI-based security systems more effective than traditional ones?
Yes, AI-based systems offer faster detection, better anomaly identification, and can reduce false positives compared to traditional setups. AI-enabled threat detection also supports automated responses that traditional rule-based systems cannot achieve.
How can organisations ensure compliance with security regulations?
By selecting solutions that provide robust monitoring, access controls, detailed audit trails, and sector-specific compliance features. Security across diverse industries must balance operational continuity with meeting all applicable regulatory obligations.
Is cloud-based security safe for sensitive environments?
Modern cloud-based security solutions offer strong encryption and central management, making them secure even for compliance-heavy sectors. Cloud security measures including access controls and audit logging are now mature enough for use in education, manufacturing, and hospitality.
What sectors benefit most from integrated security platforms?
Educational institutions, manufacturing, and hospitality experience streamlined management and enhanced safety with integrated platforms. A layered security approach that unifies physical and digital controls consistently delivers better outcomes across all three verticals.
Recommended
- Why Digital Security Matters in 2025 | Re-Solution
- Digital Security Essentials for Businesses | Re-Solution
- Cloud Security Measures & Strategies | Re-Solution