TL;DR:
- Data privacy involves managing data throughout its lifecycle, beyond just technical security measures.
- Compliance requires ongoing effort, including regular audits, staff training, and strong vendor oversight.
- Building a privacy-first culture is essential, integrating governance, policies, and leadership commitment.
Data privacy is frequently reduced to a checklist of passwords and firewalls. For IT managers in education and hospitality, this misconception carries real consequences. These sectors hold some of the most sensitive personal information in existence, from student health records to guest payment details, and the legal and operational stakes could not be higher. Understanding what data privacy actually means in an IT context, which regulations apply, and how to build lasting compliance into your organisation’s infrastructure is no longer optional. It is a core professional responsibility that directly shapes your institution’s risk profile and reputation.
Table of Contents
- Defining data privacy in IT and its core components
- Legal and regulatory frameworks shaping data privacy obligations
- Risks, real-world challenges, and what most IT leaders miss
- Building a robust data privacy culture: Steps and strategies
- The uncomfortable truths most organisations overlook about data privacy
- Upgrade your organisation’s data privacy posture
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| More than data security | Data privacy in IT requires ethical, legal, and operational stewardship beyond technical measures. |
| Laws vary by sector | Education and hospitality face different privacy rules, with special cases and exceptions to manage. |
| AI raises new risks | Modern AI tools can reveal hidden patterns, making robust governance and ongoing vigilance essential. |
| Human factors matter | Training, staff buy-in, and clear processes are just as critical as any technology implementation. |
Defining data privacy in IT and its core components
Data privacy in IT goes well beyond securing systems against external threats. It covers every stage of the data lifecycle: how information is collected, where it is stored, how it is used internally, and under what conditions it is shared with third parties. Understanding core data privacy concepts is essential before any technical controls are put in place.
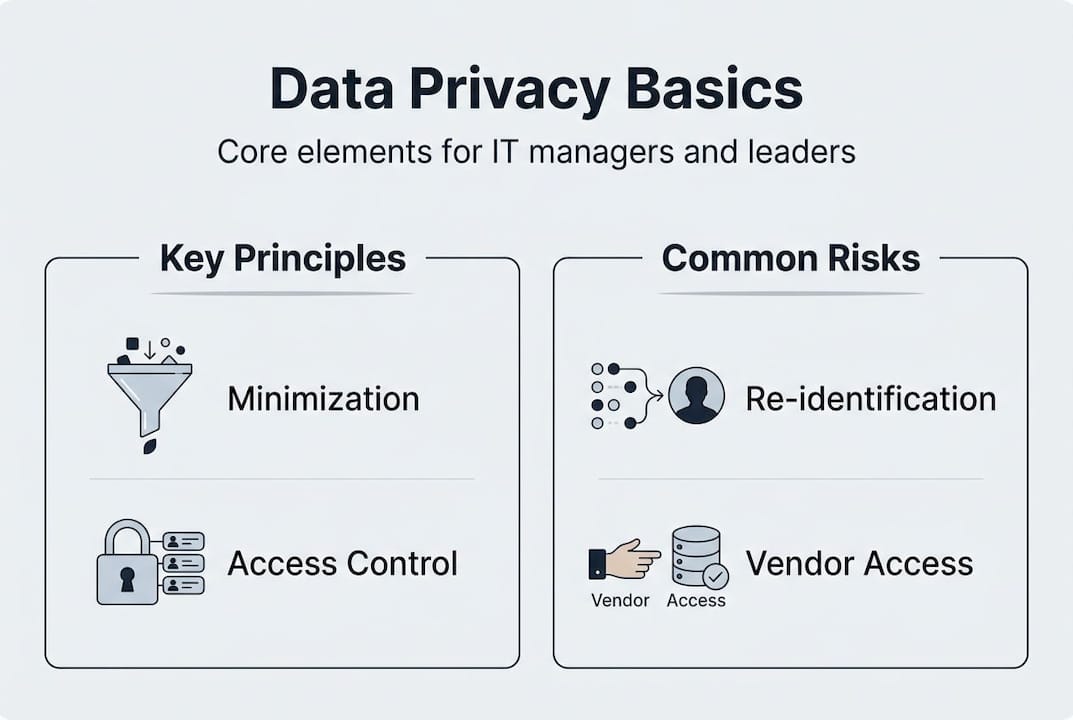
At its heart, data privacy rests on several key components:
- Personal and sensitive information: Any data that can identify an individual, directly or indirectly. This includes names, contact details, financial records, and health information.
- Consent: Individuals must, in most circumstances, actively agree to how their data is collected and used.
- Lawful processing: Data must be handled under a recognised legal basis, whether that is consent, contractual necessity, or legitimate interest.
- Rights of access and erasure: Individuals have the right to view the data held about them and request its deletion under certain conditions.
- Emerging AI governance: The growing use of analytics and AI tools introduces new obligations around how data is processed and what inferences can be drawn, an area covered in detail within AI governance in data privacy.
The types of data managed in education and hospitality differ considerably, yet both carry significant compliance obligations. The table below summarises typical data categories for each sector:
| Data category | Education examples | Hospitality examples |
|---|---|---|
| Personal identifiers | Student names, ID numbers | Guest names, passport details |
| Financial information | Fee payment records | Credit card details, billing history |
| Health and special needs | Medical conditions, SEND records | Guest allergies, mobility requirements |
| Behavioural data | Attendance, disciplinary records | Booking preferences, loyalty programme data |
| Third-party data | Parent or guardian details | Travel agent or OTA referral data |
FERPA protects student education records in the US, including how schools must manage personally identifiable information, and its principles mirror expectations in many other jurisdictions. Even where FERPA does not apply directly, its framework offers a useful benchmark for any institution handling learner data.
Pro Tip: Many organisations overlook data aggregation. Even information that appears anonymised can sometimes be re-identified when combined with other datasets, raising your legal exposure significantly.
Legal and regulatory frameworks shaping data privacy obligations
Once you understand the types of data your organisation handles, the next step is knowing which legal frameworks govern your obligations. These vary by sector and geography, but several key regulations shape day-to-day IT decisions for education and hospitality leaders.
The comparison below highlights three major frameworks:
| Framework | Sector focus | Key requirements |
|---|---|---|
| FERPA | Education (US) | Consent for record disclosure, vendor controls, parental rights |
| GDPR | All sectors (UK and EU) | Lawful basis for processing, data subject rights, breach notification |
| PCI DSS | Hospitality and retail | Secure handling of payment card data, regular security testing |
A structured approach to compliance involves three essential steps:
- Identify your requirements: Map the regulations that apply to your sector, geography, and the specific data types you hold.
- Implement controls: Put technical and procedural measures in place, including access controls, encryption, and documented consent processes.
- Audit regularly: Schedule formal reviews to ensure ongoing compliance and to catch changes in regulation or your own data practices.
One area that catches many IT leaders off guard is vendor access. FERPA has clear consent rules but exceptions and edge cases demand careful IT practice. The so-called ‘school official’ exception, which permits certain vendors to access student records without individual consent, is frequently misapplied. Without robust contractual controls and regular review, this creates real legal risk.
AI tools introduce additional complexity. AI tools can risk re-identification of data, requiring specific AI governance policies that many organisations have not yet developed. In hospitality, explicit consent is always required when processing health or dietary information, regardless of how the data was originally collected.
Staying current with data privacy regulatory requirements and mapping these to data compliance steps within your own organisation is not a one-time exercise. It is an ongoing operational commitment.
![]()
Risks, real-world challenges, and what most IT leaders miss
Knowing the legal frameworks is important, but translating compliance into operational practice is where many organisations fall short. The gap between policy and practice is where data breaches occur.
The most frequent mistakes seen in educational and hospitality IT settings include:
- Inadequate vendor oversight: Contracts are signed but vendor data practices are never reviewed again after go-live.
- Incomplete consent processes: Consent forms are generic, outdated, or do not cover the specific ways data is actually used.
- Poor data retention: Information is kept well beyond its necessary period, increasing exposure if a breach occurs.
- Uncontrolled shadow IT: Staff use unapproved tools or cloud services that sit entirely outside the organisation’s data governance framework.
- AI-driven re-identification risk: Analytical tools draw inferences from aggregated data that reveal more than originally intended.
The FERPA ‘school official’ exception is a useful illustration of this problem. It is frequently cited in vendor contracts as a justification for broad data access, yet without regular audits and precise contractual boundaries, it exposes institutions to significant liability. Legal language alone is not a substitute for active governance.
‘AI does not just analyse data; it can also reveal patterns humans miss, increasing the risk of accidental identification.’
Pro Tip: Conduct a structured vendor audit at least once per year. Review what data each supplier can access, under what conditions, and whether their own sub-processors have been disclosed. Legal agreements matter, but verified practice matters more.
Reviewing data privacy best practices alongside your existing supplier arrangements will often reveal gaps you did not know existed. For hospitality IT leaders, safeguarding customer data effectively requires the same discipline applied to guest-facing systems as it does to internal infrastructure.
Building a robust data privacy culture: Steps and strategies
With a clear view of the risks, IT decision-makers need a practical roadmap for embedding data privacy across their organisation. Technology controls alone will not get you there.
Follow these six steps to build a genuine privacy-first culture:
- Secure leadership buy-in: Data privacy cannot be treated as a purely technical matter. Senior leadership must understand the risks and commit to resourcing compliance adequately.
- Map your data flows: Document what data you hold, where it comes from, how it moves through your systems, and where it goes. This record of processing activities is required under GDPR.
- Apply privacy by design: Build privacy considerations into new systems and processes from the outset, rather than retrofitting controls after the fact.
- Update policies and procedures: Ensure your acceptable use, data retention, and incident response policies reflect current regulations and your actual IT estate.
- Train staff regularly: Edge cases, overlapping regulations, and staff training all demand ongoing attention. Annual training is a minimum, not a ceiling.
- Run simulated incidents: Practise your response to a data breach before one happens. This reveals gaps in escalation channels and decision-making that table-top exercises alone cannot surface.
Essential policies and processes to maintain include:
- A record of processing activities (ROPA) kept up to date
- Regular internal and external audits of data practices
- Clear escalation channels for suspected breaches
- Defined data retention and deletion schedules
- Privacy impact assessments for new projects or technologies
For guidance on securing sensitive data at the infrastructure level, and for institutions seeking sector-specific frameworks, PII security in education provides targeted starting points. The critical lesson is that human processes and technical controls must work together. One without the other creates blind spots.
The uncomfortable truths most organisations overlook about data privacy
After years of working with organisations across education and hospitality, we have observed a consistent pattern: most IT leaders understand the regulations in theory but underestimate the complexity in practice. Data aggregation and re-identification are still treated as edge cases, when modern AI tools have made them a mainstream risk.
The most persistent myth is that passing a compliance audit equals safety. It does not. Audit frameworks capture a snapshot in time. Real data privacy requires active governance, which means continuously questioning your assumptions, reviewing vendor relationships, and updating controls as your data environment changes.
Privacy by design remains genuinely rare. Most organisations still retrofit controls after systems have been built, which is far more costly and far less effective. This will shape IT investment decisions for years to come as regulators increase scrutiny and enforcement. Understanding why privacy goes beyond compliance is the first step toward building something that actually holds up under pressure. Compliance is the floor, not the ceiling.
Upgrade your organisation’s data privacy posture
For IT leaders ready to move beyond theory and strengthen their organisation’s approach to data privacy, the right infrastructure and expert guidance make a measurable difference.
Re-Solution offers IT infrastructure and security solutions tailored to the specific compliance demands of education and hospitality. Whether you are looking to optimise network compliance, develop a clearer picture of your current environment, or explore what IT infrastructure explained means for your sector, we have the experience to support you. With over 35 years as a trusted Cisco partner, we work alongside IT teams to close the gap between compliance policy and operational reality. Speak to a specialist to discuss your organisation’s data privacy requirements.
Frequently asked questions
What counts as personal data in education and hospitality?
Personal data includes any information that can identify an individual, whether directly or in combination with other data. In practice, this covers student grades, health records, guest medical needs, and even booking preferences.
Do we always need consent to use or share data?
Explicit consent is usually required, but strict controls under FERPA and GDPR include defined exceptions, such as FERPA’s ‘school official’ clause, which permits limited vendor access under specific conditions.
How do AI tools affect data privacy risks?
AI models can re-identify aggregated or anonymised data by identifying patterns across datasets, which significantly increases privacy risk and demands specific governance policies.
What is the most common mistake IT teams make in data privacy compliance?
FERPA’s vendor oversight edge cases illustrate a broader problem: many IT teams rely on technical controls and legal language while neglecting active vendor audits and ongoing staff training.
Recommended
- Data privacy best practices for education and manufacturing
- Why Data Security Matters in 2025 | Re-Solution
- Data Privacy Challenges to Watch in 2025 | Re-Solution





