TL;DR:
- Effective cloud adoption requires meticulous architecture, security governance, and ongoing operational assessment beyond simple workload migration.
- Prioritizing configuration governance, network segmentation, and continuous validation ensures long-term security and compliance success in cloud environments.
Cloud adoption is rarely as straightforward as vendors suggest. Many IT teams at educational institutions and manufacturing companies discover that simply migrating workloads to a cloud provider does not, by itself, deliver the security, connectivity, or compliance outcomes they need. The real complexity lies in configuration governance, network architecture decisions, and continuous operational assessment. This guide addresses those realities directly, offering structured guidance on reference architecture, security frameworks, migration methodology, IoT security, and benchmarking so that your organisation can build a cloud environment that genuinely performs under operational pressure.
Table of Contents
- Setting up cloud infrastructure: Reference architecture and production parity
- Security and compliance: Governance, standards, and operational risks
- Migration methodology: Connectivity scenarios and service equivalence
- Industrial and educational connectivity: Edge cases and IoT security
- Empirical benchmarking and ongoing assessment: Measuring operational impact
- Why configuration governance, not platform choice, dictates your cloud success
- Start your journey with proven cloud-based infrastructure solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Architecture matters most | Proper network segregation and high availability design directly impact long-term cloud success. |
| Security requires structure | Benchmarks like CIS and NIST ensure governance and operational controls actually work in practice. |
| Migration needs scenario planning | Mapping service equivalents and planning for latency-sensitive dependencies smooths the migration process. |
| IoT security must be continuous | Device authentication and ongoing protocol validation are vital for edge environments in industry and education. |
| Continuous benchmarking drives improvement | Telemetry-based assessments provide actionable feedback and prevent outdated security controls. |
Setting up cloud infrastructure: Reference architecture and production parity
With misconceptions addressed, the critical first step is building the right cloud architecture from the ground up. Rushing past this stage is one of the most common and costly mistakes IT teams make.
A practical starting point involves three foundational mechanics. Going to production on cloud infrastructure requires segregating networks into public and private segments, mirroring environments for production parity, and planning for high availability across availability zones. These are not optional refinements. They are structural requirements for a stable production environment.
For educational institutions, this means isolating student-facing wireless networks from administrative systems and research platforms. For manufacturing companies, it means keeping operational technology (OT) traffic separated from corporate IT systems to reduce the blast radius of any security incident.
Key architectural principles to establish early:
- Separate public-facing services (web portals, VPNs) from internal workloads using clearly defined network segments
- Mirror development, staging, and production environments to catch configuration drift before it reaches live systems
- Deploy workloads across multiple availability zones to maintain service continuity during outages
- Use infrastructure-as-code tooling to enforce consistency and reduce manual configuration errors
- Review future-proof IT infrastructure considerations before committing to a single architectural pattern
Comparison: Common cloud architecture approaches
| Approach | Benefit | Risk if skipped |
|---|---|---|
| Public/private segmentation | Limits lateral movement by attackers | Flat networks expose all systems equally |
| Production parity (env mirroring) | Reduces deployment surprises | Configuration gaps cause outages |
| Multi-zone high availability | Maintains uptime during zone failures | Single-zone deployments fail silently |
| Infrastructure-as-code | Enforces repeatable, auditable builds | Manual builds introduce drift and inconsistency |
Understanding cloud networking basics before finalising your architecture will save significant remediation effort later. Teams that treat architecture as a one-time decision rather than a continuous engineering discipline tend to accumulate technical debt rapidly.
For AWS migration for secure infrastructure, specific guidance around VPC design and subnet allocation provides a practical reference for organisations building their first production-grade cloud environment.
Pro Tip: Always validate your network segmentation rules in a staging environment that mirrors production exactly. Misconfigured security groups and access control lists are among the leading causes of unintended data exposure in cloud deployments.
Security and compliance: Governance, standards, and operational risks
Once the foundational architecture is built, security and regulatory compliance become vital for ongoing operation and continued assurance. This is where many organisations underestimate the effort involved.

Cloud security assessments must explicitly account for the cloud shared-responsibility model, multi-cloud dynamics, and dynamic configuration risks. The shared-responsibility model means the cloud provider secures the underlying infrastructure, but your organisation remains responsible for everything above it: data, identity, network configuration, and application controls. Misunderstanding this boundary is a recurring source of compliance failures.
For educational institutions subject to UK GDPR and sector-specific data protection requirements, and for manufacturing companies operating under ISO 27001 or industry-specific standards, the compliance burden is significant. Both sectors must demonstrate evidence-based controls, not simply contractual assurances.
Structured steps for cloud security governance:
- Map your regulatory obligations to specific technical controls (encryption, access control, logging)
- Apply CIS Benchmarks and NIST frameworks to assess your baseline security posture
- Enable encryption at rest and in transit for all regulated data stores
- Enforce network isolation between workloads handling sensitive data and general-purpose systems
- Implement continuous configuration monitoring to detect policy drift between audit cycles
- Document evidence of control effectiveness for audit readiness
“Cloud compliance issues commonly stem from incorrect configuration rather than underlying infrastructure failures. Encryption and network isolation are the central mechanics that regulators examine first.”
The Azure Microsoft Cloud Security Benchmark (MCSB) and AWS Security Hub both provide built-in policy checks that map to these frameworks. Using them reduces the manual overhead of compliance evidence gathering considerably.
For cloud security for AWS migrations, additional guidance covers how to maintain security posture during the migration process itself, which is a period of elevated risk that many teams neglect to plan for explicitly.
Reviewing a thorough network security guide alongside your cloud security strategy ensures that on-premises and cloud controls are aligned, rather than creating gaps at the boundary between environments.
Pro Tip: Policy checks confirm what your configuration says it does. Operational validation confirms what your configuration actually does. Run both. Automated policy scanning and manual penetration testing serve different and complementary purposes.
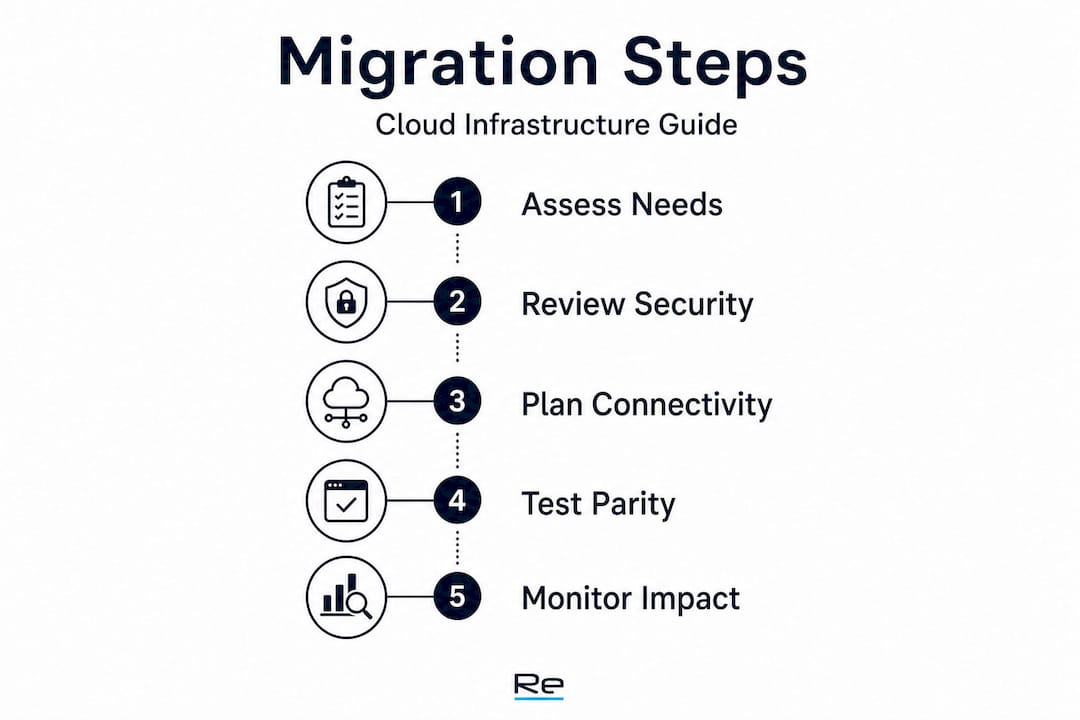
Migration methodology: Connectivity scenarios and service equivalence
With security and compliance frameworks in place, the focus shifts to operational migration strategies and connectivity scenarios for seamless cloud adoption.
Migration is not a single event. It is a structured programme of work that requires careful sequencing, especially when networking elements are involved. Latency-sensitive dependencies, such as database connections in manufacturing execution systems or real-time assessment platforms in education, require specific architectural decisions before workloads move.
AWS prescriptive migration guidance explicitly identifies latency-sensitive dependencies and IT shared services coordination as migration challenges that must be planned for at scale. Ignoring these during the planning phase results in performance degradation and rollback events that erode confidence in the migration programme.
Networking migration deserves its own workstream. You should identify service equivalents across providers, matching VPCs to VNets, comparing load balancer capabilities, and aligning firewall rule sets, before moving any workloads. Connectivity scenarios including site-to-site VPN, BGP peering, and load balancer migrations must each have documented runbooks.
Critical connectivity decisions during migration:
- Determine whether site-to-site VPN or dedicated connectivity (such as AWS Direct Connect or Azure ExpressRoute) is appropriate for latency-sensitive workloads
- Document BGP routing configurations and validate failover behaviour before cutover
- Align load balancer configurations between source and target environments to prevent traffic distribution issues
- Plan DNS cutover timing carefully to avoid extended propagation delays affecting users
Networking service comparison: AWS vs Azure
| Service category | AWS equivalent | Azure equivalent | Key consideration |
|---|---|---|---|
| Virtual network | VPC | VNet | CIDR overlap must be avoided in hybrid designs |
| Load balancing | ALB / NLB | Application Gateway / Load Balancer | Feature parity varies; validate health check behaviour |
| Firewall | AWS Network Firewall | Azure Firewall | Rule migration requires manual review |
| VPN connectivity | AWS Site-to-Site VPN | Azure VPN Gateway | BGP support and bandwidth caps differ |
| Private connectivity | AWS Direct Connect | Azure ExpressRoute | Lead times for physical provisioning can be 4 to 8 weeks |
Understanding infrastructure migration challenges before you begin will help your team set realistic timelines and avoid scope creep. Following AWS migration best practices for sequencing workloads and validating connectivity at each stage reduces the likelihood of cascading failures during cutover windows.
Industrial and educational connectivity: Edge cases and IoT security
Operational environments introduce unique connectivity and edge-case security demands, particularly for IoT devices deployed across industrial and educational settings.
Manufacturing facilities and school campuses share a common challenge: large numbers of connected devices operating across physically distributed locations, often with heterogeneous operating systems and inconsistent patch histories. Securing these environments requires more than perimeter-based controls.
Volkswagen’s industrial cloud, which connects 122 factories worldwide, demonstrates the architecture pattern that large-scale operational deployments require: secure device-to-cloud transport using MQTT over TLS 1.3, strong device identity through X.509 certificates, and continuous authentication to validate device integrity throughout the session, not just at the point of connection.
IoT security implementation checklist:
- Assign a unique X.509 digital certificate to every device connecting to the cloud environment
- Enforce MQTT over TLS 1.3 (or HTTPS where MQTT is not appropriate) for all device-to-cloud communication
- Implement continuous authentication so that compromised devices are revoked mid-session without manual intervention
- Segment IoT device traffic into dedicated network zones separate from user and server traffic
- Apply allowlist-based firewall policies that permit only expected device communication patterns
- Conduct regular firmware audits to identify devices running out-of-support software
Reviewing secure network design examples provides practical reference architectures for isolating IoT traffic and applying Zero Trust posture to device connections in both industrial and campus environments.
Pro Tip: Adopt a Zero Trust posture for every device connection. Treat each connection attempt as untrusted by default, verify device identity continuously, and enforce least-privilege access to cloud resources regardless of where the device is physically located.
Empirical benchmarking and ongoing assessment: Measuring operational impact
Securing edge environments and IoT connectivity leads directly to the need for ongoing real-world assessment and benchmarking for operational assurance.
Deploying controls is not enough. IT teams must be able to demonstrate that those controls work under realistic conditions. This is especially important for organisations undergoing external audits or responding to incidents.
Benchmarking cloud security platforms effectively requires building telemetry-driven tests that simulate attacker progression and capture detection, triage, and response timing across the full kill chain. These tests produce objective metrics that policy reviews simply cannot generate.
Key metrics to capture during security benchmarking:
- Time to detect (TTD): How quickly does your tooling identify a malicious event after it occurs?
- Time to classify (TTC): How long does it take to determine the severity and scope of a detected event?
- Time to respond (TTR): How long from detection to containment or remediation?
- False positive rate: What proportion of alerts are non-events that consume analyst time?
- Control coverage: What percentage of MITRE ATT&CK techniques are detected by your current toolset?
These metrics provide actionable feedback for evidence-driven governance. If your TTD is measured in hours rather than minutes, that is a measurable risk that requires a specific remediation investment.
Reviewing your cloud security measures against benchmarking results gives IT leadership a defensible position in risk review meetings and provides a clear baseline for demonstrating improvement over time.
Pro Tip: Continuous benchmarking prevents outdated controls from persisting undetected. Schedule quarterly simulation exercises that mirror current threat intelligence, not last year’s attack patterns. Cloud environments change rapidly, and controls that were effective six months ago may have been bypassed by configuration drift.
Why configuration governance, not platform choice, dictates your cloud success
Having covered practical mechanics and benchmarking, it is worth stepping back to reconsider what truly drives long-term cloud success for IT leadership. The answer is less comfortable than most vendor conversations suggest.
Organisations routinely spend considerable effort evaluating cloud providers, comparing pricing models, and negotiating enterprise agreements. That effort has value. But the evidence consistently points to a different factor as the primary driver of cloud security and compliance outcomes: configuration governance.
HIPAA-compliant workloads in the cloud fail not because the provider’s infrastructure is inadequate, but because encryption is not enabled, network isolation is not enforced, or access controls are too permissive. The same pattern appears across UK data protection investigations, ISO 27001 audits, and Cyber Essentials assessments. The finding is almost always a configuration problem, not a platform problem.
This means that an organisation running a well-governed environment on a second-tier cloud provider will consistently outperform one running poorly governed workloads on a market-leading platform. Platform reputation does not substitute for operational discipline.
The practical implication for IT decision-makers is this: invest proportionally in governance tooling, configuration review processes, and operational validation. Automated policy scanning, regular third-party audits, and structured change management processes are not overhead. They are the core of your cloud security programme.
Reviewing a structured IT compliance guide tailored to education and manufacturing will help your team understand where configuration gaps most commonly appear in your sector and how to build review cycles that catch drift before it becomes a reportable incident.
Audit readiness starts with practical evidence, not contract assurances. Document what your controls actually do, test them under realistic conditions, and maintain that evidence continuously rather than assembling it in the weeks before an audit.
Start your journey with proven cloud-based infrastructure solutions
After covering the architecture, security, migration, and governance mechanics that underpin successful cloud adoption, the next step is working with specialists who have the depth of experience to apply these principles in your specific environment.
Re-Solution has supported educational institutions and manufacturing companies for over 35 years, delivering Cisco-based network and security solutions that address exactly the challenges outlined in this guide. From network as a service models that simplify connectivity management to structured infrastructure audits that identify configuration risks before they become incidents, Re-Solution brings the operational rigour that cloud adoption demands. If you are ready to move beyond generic cloud checklists and build an environment grounded in IT infrastructure best practice, speak with our team to explore the right approach for your organisation.
Frequently asked questions
What are the key steps to designing secure cloud infrastructure?
Segregating public and private network segments, mirroring environments for production parity, and planning for high availability across availability zones are the foundational steps for any production-grade cloud design.
Which security frameworks are most relevant for cloud infrastructure?
CIS Benchmarks and NIST are the most widely adopted standards for securing operating systems, networks, and cloud service providers, and they provide a measurable baseline for ongoing compliance assessment.
How do you handle compliance for regulated workloads in the cloud?
Cloud compliance failures most commonly result from incorrect configuration rather than platform inadequacy, so focus on enabling encryption, enforcing network isolation, and validating controls operationally rather than relying on contractual assurances.
What is the best approach to cloud migration for networking elements?
Identify equivalent networking services across your source and target platforms and document connectivity scenarios using structured migration runbooks before moving any workloads, particularly for latency-sensitive dependencies.
How can IT teams measure the effectiveness of their cloud security?
Telemetry-driven attack simulations that capture detection, classification, and response timings provide objective evidence of control effectiveness and highlight gaps that policy reviews alone cannot surface.
Recommended
- Understanding Cloud Networking: Expert Guide | Re-Solution
- Understanding Cloud Networking: Expert Guide | Re-Solution
- How to Future-Proof IT Infrastructure for 2025 | Re-Solution





