TL;DR:
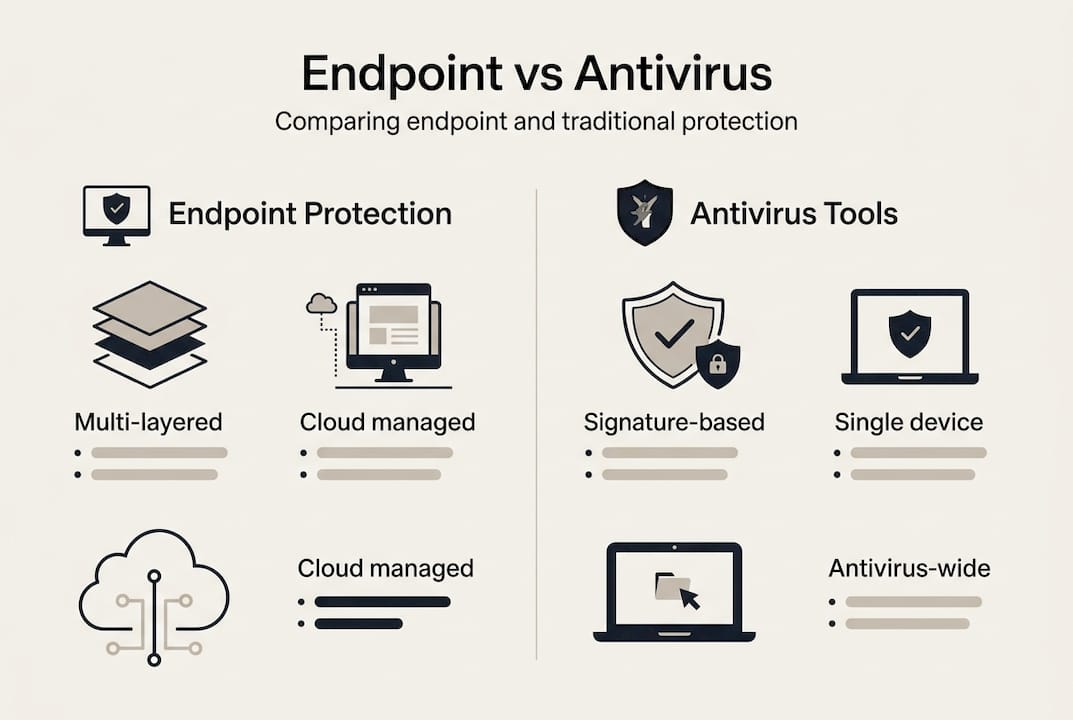
- Traditional antivirus tools are insufficient against modern sophisticated cyber threats targeting diverse devices.
- Endpoint protection platforms use AI, behavioural analysis, and central management to detect and block threats proactively.
- Effective endpoint security requires ongoing management, staff training, and regular audits to prevent breaches and ensure compliance.
Relying on standard antivirus to protect your organisation’s devices is no longer sufficient. Cyber threats have grown far more sophisticated, targeting endpoints such as laptops, tablets, and mobiles with precision that legacy tools simply cannot match. For IT managers in educational institutions and manufacturing companies, this gap in protection carries serious consequences, from data breaches to regulatory fines. This guide explains what endpoint protection is, how it works, and why it should form the foundation of any modern cybersecurity strategy. You will also find practical comparisons, feature breakdowns, and clear guidance on applying these solutions to your specific environment.
Table of Contents
- Defining endpoint protection and its core purpose
- How endpoint protection works: technologies and features
- Endpoint protection vs. traditional cybersecurity tools
- Why endpoint protection matters: risks, compliance, and organisational benefits
- A fresh perspective: the overlooked essentials for effective endpoint defence
- Enhance your cybersecurity with expert-driven solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive endpoint security | Modern endpoint protection offers layered defences beyond antivirus to secure all devices accessing your network. |
| Supports compliance | Implementing endpoint protection helps meet regulatory requirements and reduces organisational risk. |
| Holistic approach | Success relies on technology, regular management, and user education working together. |
| Tailored for organisations | Endpoint protection is particularly vital in education and manufacturing due to device variety and sensitive data. |
Defining endpoint protection and its core purpose
Endpoint protection is a cybersecurity discipline focused on securing every device that connects to your organisation’s network. This includes laptops, desktop computers, mobile phones, tablets, and increasingly, Internet of Things (IoT) devices found in manufacturing environments. Each of these represents a potential entry point for attackers, which is why protecting them collectively is now a priority rather than an afterthought.
Traditional antivirus software was designed for a different era. It works by scanning files against a database of known malware signatures. If the threat is not in the database, it goes undetected. Modern threats, including fileless malware, zero-day exploits, and ransomware, do not follow predictable patterns. They are built to evade signature-based detection entirely.
Endpoint protection platforms (EPPs) take a fundamentally different approach. As endpoint security definition describes it, endpoint security extends beyond antivirus and includes a range of monitoring, detection, and remediation tools. This layered approach addresses threats at multiple stages, before, during, and after an attack.
Core functions of an endpoint protection solution include:
- Threat detection: Identifies known and unknown threats using behavioural analysis and threat intelligence
- Real-time monitoring: Continuously observes device activity to flag anomalies the moment they occur
- Automated remediation: Isolates compromised devices and removes threats without manual intervention
- Centralised reporting: Provides IT teams with a single dashboard view across all endpoints
- Policy enforcement: Applies consistent security rules across every device in the network
For educational institutions, the device landscape is particularly varied. Students bring personal laptops, staff use shared desktops, and admin teams handle sensitive student records on mobile devices. Manufacturing companies face a similar challenge with a mix of legacy systems, production terminals, and office workstations all sitting on the same network. Understanding digital security essentials for these environments is the first step toward meaningful protection.
Endpoints are the most exposed part of any organisation’s infrastructure. Without a unified protection strategy, every unmanaged device becomes a potential liability.
How endpoint protection works: technologies and features
Endpoint protection solutions operate through a combination of layered technologies, each addressing a specific threat vector. Understanding these components helps IT managers evaluate what a platform actually delivers, rather than accepting vendor claims at face value.

Next-generation endpoint security platforms use AI, behaviour analysis, firewall, and encryption for comprehensive defence. These technologies work together to cover gaps that any single tool would leave open.
| Feature | Standard antivirus | Endpoint protection platform |
|---|---|---|
| Signature-based detection | Yes | Yes |
| Behavioural analysis | No | Yes |
| AI and machine learning | No | Yes |
| Firewall integration | Limited | Full |
| Device encryption | No | Yes |
| Centralised management | No | Yes |
| Incident response tools | No | Yes |
| Remote device control | No | Yes |
Here is how an endpoint protection solution handles a threat from start to finish:
- Detection: The platform identifies suspicious activity using AI-driven behavioural analysis, not just known signatures
- Analysis: The threat is assessed in a sandboxed environment to determine its nature and scope
- Containment: The affected device is automatically isolated from the network to prevent lateral spread
- Remediation: Malicious files are removed and affected systems are restored to a clean state
- Reporting: A full incident log is generated for audit purposes and future threat intelligence
In manufacturing environments, where operational technology (OT) and information technology (IT) networks often intersect, this step-by-step response is critical. A breach that begins on a factory terminal can quickly reach sensitive design files or financial systems if left unchecked. For educational institutions, the same logic applies across student portals, learning management systems, and staff devices.
Understanding the difference between antivirus vs anti-malware tools is also useful context here. Many organisations assume they are protected when they only have one layer of defence in place.
Pro Tip: Do not overlook mobile devices and remote endpoints. With hybrid working now standard across many sectors, unmanaged personal devices accessing school or factory systems represent one of the largest unaddressed risks in most organisations.
Endpoint protection vs. traditional cybersecurity tools
With a clear picture of how endpoint protection works, it is worth comparing it directly to the tools many organisations still rely on. The distinction matters because IT budgets are finite, and understanding where traditional tools fall short helps justify the investment in a more capable platform.
Endpoint protection consolidates multiple layers beyond antivirus and adapts to a rapidly changing threat landscape. Legacy tools were built for a time when threats were slower, simpler, and more predictable.
| Capability | Antivirus | Basic firewall | Endpoint protection platform |
|---|---|---|---|
| Known threat detection | Yes | Partial | Yes |
| Unknown threat detection | No | No | Yes |
| Centralised management | No | No | Yes |
| User behaviour analytics | No | No | Yes |
| Encryption and data control | No | No | Yes |
| Compliance reporting | No | No | Yes |
| Scalability | Limited | Limited | High |
Key advantages that endpoint protection platforms deliver over traditional tools include:
- Agility: Rapidly adapts policies in response to emerging threats without manual reconfiguration
- Threat intelligence feeds: Pulls real-time data from global threat databases to stay ahead of attacks
- Centralised control: Manages all devices from a single console, reducing administrative overhead
- Scalability: Easily accommodates new devices as organisations grow or adopt remote working
For organisations managing a high volume of devices, such as a secondary school with hundreds of student laptops or a factory floor with dozens of terminals, these capabilities are not optional extras. They are operational necessities. Reviewing network security best practices alongside endpoint protection ensures a joined-up approach.
Pro Tip: One of the most common and costly mistakes is relying solely on antivirus as a tick-box exercise. Attackers actively probe for organisations using minimal protection. Upgrading to an endpoint protection platform signals to your incident response team and your insurers that security is taken seriously.
Why endpoint protection matters: risks, compliance, and organisational benefits
Endpoints are not just a technical concern. They sit at the intersection of operational risk, regulatory compliance, and organisational reputation. For IT decision-makers, understanding the real-world consequences of inadequate endpoint protection is essential for building a business case internally.
Common endpoint threats facing educational institutions and manufacturing companies include:
- Ransomware: Encrypts critical files and demands payment, causing significant downtime
- Phishing attacks: Targets staff and students via email to harvest credentials or deploy malware
- Device theft: Lost or stolen laptops expose sensitive data without proper encryption
- Unauthorised access: Unmanaged devices connecting to the network create open doors for attackers
- Supply chain attacks: Third-party software updates used as vectors to infiltrate network systems
Endpoint attacks are responsible for a significant percentage of breaches, often due to device vulnerabilities that go unpatched or unmonitored.
The majority of successful cyber attacks originate at the endpoint. Most are preventable with the right controls in place.
From a compliance perspective, endpoint protection is not simply good practice. It is increasingly a regulatory requirement. GDPR mandates that organisations implement appropriate technical measures to protect personal data. For schools holding student records and manufacturers holding employee or client information, demonstrable endpoint controls directly support compliance obligations.
Organisational benefits of endpoint protection extend well beyond avoiding breaches:
- Reduced incident response time: Automated detection and containment means threats are neutralised faster
- Audit-ready reporting: Centralised logs provide evidence of security controls for regulatory audits
- Operational continuity: Rapid remediation minimises downtime on production lines or school networks
- Staff confidence: Clear security controls reduce the risk of accidental data exposure by end users
For manufacturing companies, proprietary designs, production schedules, and supplier contracts represent intellectual property worth protecting. For educational institutions, the data held on students, including safeguarding records, is among the most sensitive in any sector. Strengthening your approach to network security essentials sits alongside endpoint protection as a core organisational priority.
A fresh perspective: the overlooked essentials for effective endpoint defence
Most conversations about endpoint protection focus on platforms, features, and pricing. That is understandable, but it misses a critical part of the picture. Technology alone does not secure endpoints. Configuration, ongoing management, and staff awareness are just as important, and far more often neglected.
We see this regularly across education and manufacturing clients. An organisation invests in a capable endpoint protection platform, then deploys it with default settings, assigns one person to manage it alongside fifteen other responsibilities, and provides no training to staff. The platform is in place, but the protection is superficial.
Effective endpoint defence is a process, not a product. Policies must be aligned with the platform’s capabilities. User training must address the actual behaviours that create risk, such as clicking unknown links or connecting personal devices to the work network. Incident response procedures must be tested regularly, not just documented.
The organisations that get this right treat endpoint protection as an ongoing programme with regular reviews and clear ownership. Reviewing IT security improvement tips as part of that programme keeps your approach current.
Pro Tip: Establish a quarterly endpoint audit routine. Review which devices are enrolled, check for policy drift, and validate that updates are being applied consistently. Small, regular checks prevent the gradual erosion of protection that leaves organisations exposed.
Enhance your cybersecurity with expert-driven solutions
Evaluating your current endpoint security posture is the most important first step you can take. Many organisations discover gaps only after an incident, which is far more costly than a proactive review.
At Re-Solution, we help IT managers in education and manufacturing assess, implement, and maintain robust endpoint protection as part of a wider security strategy. Our managed IT services provide ongoing monitoring and management so your endpoints are never left unguarded. If you are unsure where your current vulnerabilities lie, our network audit services deliver a clear, expert view of your infrastructure and a prioritised plan for improvement. Get in touch to take the next step.
Frequently asked questions
What are endpoints in cyber security?
Endpoints are individual devices such as desktops, laptops, tablets, or mobiles that connect to your network and require protection from external and internal threats.
Does endpoint protection include antivirus?
Yes, most endpoint protection solutions include antivirus but also offer additional layers. Endpoint protection platforms consolidate antivirus with firewall integration, intrusion prevention, behavioural analysis, and more.
Why is endpoint protection important for compliance?
Endpoint protection helps prevent unauthorised data access and ensures the technical controls required by regulations like GDPR are in place. Endpoint protection assists with demonstrable compliance during audits and incident investigations.
Can endpoint protection support remote work environments?
Yes, endpoint protection covers devices both on-premises and remote. Remote device management is a core function of modern endpoint protection services, ensuring consistent policy enforcement regardless of device location.
Recommended
- 2025 Data Protection Strategies You Need | Re-Solution
- Essential Guide: How to Secure Sensitive Data Fast | Cisco Cloud, Security & Datacenter Experts
- Best Practices for Data Protection 2025 | Re-Solution





