Security incidents affect 82% of K-12 schools, yet many IT managers struggle to identify which security services genuinely protect their infrastructure. The confusion stems from fragmented advice and generic solutions that ignore sector-specific threats. This comprehensive overview clarifies security services tailored to education, manufacturing, logistics, hospitality, and property development sectors. You will discover frameworks that align with your operational realities, technologies that integrate physical and cyber defences, and methodologies proven to reduce vulnerabilities across diverse environments.
Table of Contents
- Key takeaways
- Security services for education infrastructure
- Combined physical and cyber security in manufacturing and logistics
- Tailored security services for hospitality and property development
- Core methodologies and frameworks underpinning security services
- Explore tailored security solutions with Re-Solution
- Frequently asked questions about security services
Key Takeaways
| Point | Details |
|---|---|
| NIST CSF alignment | Adopt the NIST Cybersecurity Framework across identify protect detect respond and recover to align controls and prioritise remediation by risk. |
| Ransomware defences | Implement multi layer defences including immutable backups with offline copies tested quarterly, email filtering, endpoint detection and response, and user awareness training to recognise phishing. |
| MSSP support | Managed Security Service Providers fill staffing gaps in education, delivering continuous monitoring, threat intelligence analysis and 24/7 incident response. |
| AI security uplift | Emerging technologies including AI can strengthen physical security and enhance threat detection across combined cyber and physical layers. |
| Purdue Model guidance | Manufacturing and logistics benefit from combined physical and cyber controls guided by the Purdue Model for OT IT segmentation. |
Security services for education infrastructure
Educational institutions face relentless cyber threats whilst managing constrained budgets and limited IT staff. Network security fundamentals form the foundation: next-generation firewalls inspect traffic at application layers, network segmentation isolates student devices from administrative systems, and identity-based access controls restrict sensitive data exposure. Cloud and SaaS protections extend these controls beyond campus perimeters as schools adopt hybrid learning platforms.
Compliance obligations shape security architecture. FERPA and COPPA mandate strict student data protections, whilst the NIST Cybersecurity Framework structures implementation across five phases: identify, protect, detect, respond, and recover. Schools map existing controls to framework categories, identify gaps, then prioritise remediation based on risk assessments. This structured approach satisfies auditors and focuses limited resources on high-impact improvements.
Ransomware protection demands urgent attention given incident prevalence. Multi-layered defences include:
- Automated backup systems with immutable storage and offline copies tested quarterly
- Email filtering that blocks malicious attachments and quarantines suspicious links before reaching inboxes
- Endpoint detection and response tools that isolate infected devices within seconds
- User awareness training targeting phishing recognition and safe browsing habits
- Incident response playbooks defining communication protocols and recovery procedures
Managed Security Service Providers fill critical staffing gaps. Few K-12 districts employ dedicated cybersecurity professionals, making MSSPs essential for continuous monitoring, threat intelligence analysis, and 24/7 incident response. These providers deploy Security Operations Centre analysts who correlate alerts across firewalls, intrusion detection systems, and endpoint agents, distinguishing genuine threats from benign anomalies.
Pro Tip: Schedule tabletop exercises simulating ransomware scenarios with staff, testing communication chains and backup restoration procedures before real incidents create chaos.
Best practices emphasise proactive detection over reactive cleanup. Security Information and Event Management platforms aggregate logs from network devices, servers, and applications, applying correlation rules that flag unusual patterns like after-hours database queries or privilege escalation attempts. Threat intelligence feeds provide indicators of compromise specific to education sector attacks, enabling preemptive blocking of known malicious infrastructure.
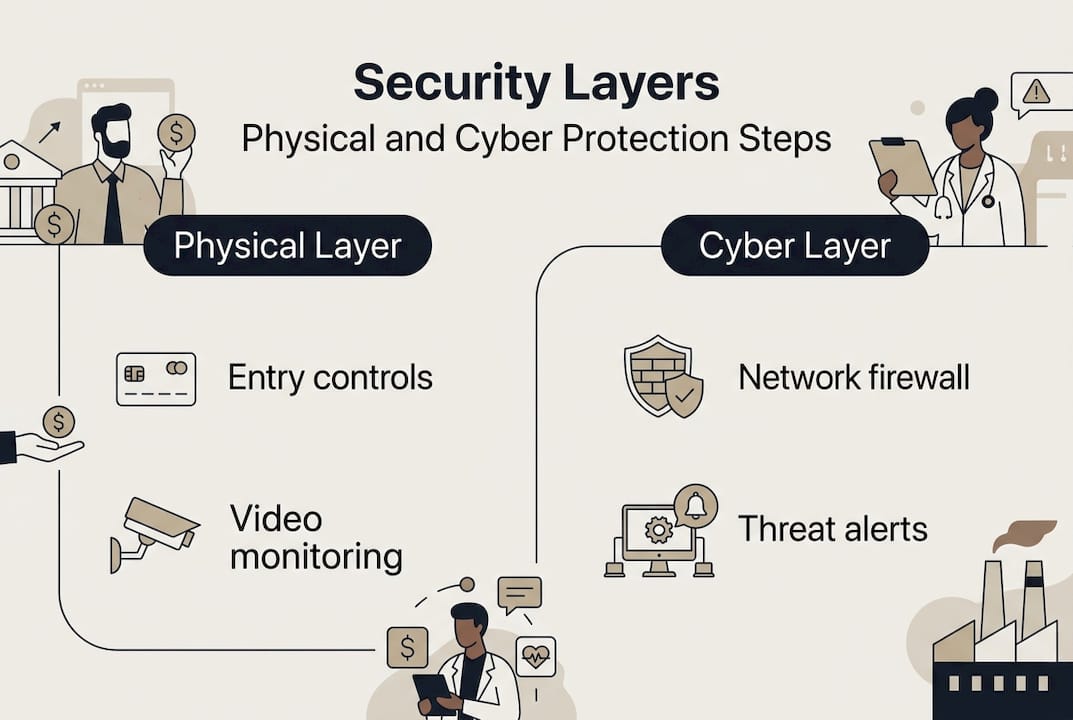
Combined physical and cyber security in manufacturing and logistics
Manufacturing and logistics operations require integrated security addressing both physical sites and interconnected operational technology. Physical controls establish the first defence layer: perimeter fencing with intrusion detection sensors, strategically positioned CCTV cameras covering loading docks and production floors, biometric access systems restricting entry to authorised personnel, and roving security patrols deterring opportunistic threats. These measures reduce attack surface by 75% when properly coordinated.
Cyber controls protect industrial systems from network-borne threats. The Purdue Model guides OT/IT segmentation, creating distinct zones that isolate process control networks from enterprise systems. Firewalls between zones enforce strict traffic rules, permitting only essential communications whilst blocking lateral movement by attackers. NIST Cybersecurity Framework principles extend to operational technology, with asset inventories documenting every programmable logic controller, human-machine interface, and SCADA system.
| Security layer | Purpose | Technology | Benefits |
|---|---|---|---|
| Physical perimeter | Prevent unauthorised site access | Fencing, gates, CCTV, motion sensors | Deters intruders, provides evidence, controls entry points |
| Cyber segmentation | Isolate OT from IT networks | Firewalls, VLANs, air gaps | Limits breach propagation, protects production systems |
| Surveillance integration | Correlate physical and digital events | Video analytics, SIEM platforms | Identifies coordinated attacks, reduces investigation time |
| Managed detection | Continuous threat monitoring | MDR services, SOC analysts | Lowers mean time to detect by 23%, expert response |
Integrated video surveillance transforms passive recording into active threat detection. Modern systems apply analytics recognising unusual behaviours like loitering near restricted areas, vehicles entering through exit lanes, or individuals accessing facilities outside scheduled shifts. Integration with access control platforms triggers alerts when doors open without valid credentials, whilst SIEM correlation identifies potential insider threats exhibiting both physical and cyber anomalies.
Industrial security guards provide human intelligence that technology cannot replicate. Trained personnel recognise social engineering attempts, verify contractor identities beyond badge scans, and respond to ambiguous situations requiring judgement. Their presence reduces workplace violence, theft, and safety incidents whilst supporting regulatory compliance in sectors like chemicals and pharmaceuticals. The manned security market exceeds $67 billion, reflecting persistent demand for human oversight.
Managed Detection and Response services address the complexity of monitoring diverse security tools. MDR providers deploy sensors across IT and OT environments, analysing network traffic, endpoint behaviours, and system logs for indicators of compromise. Their analysts investigate alerts, eliminating false positives and escalating genuine threats with context-rich reports. This approach reduces mean time to detect sophisticated attacks, particularly those exploiting OT vulnerabilities absent from traditional IT security tools.
Pro Tip: Prioritise OT visibility by deploying passive network monitoring that inspects industrial protocols without disrupting production, revealing unauthorised devices and configuration changes attackers exploit.
Logistics facilities face unique challenges from high personnel turnover and transient contractor access. Temporary workers require rapid credential provisioning and revocation, whilst delivery drivers need limited access to loading areas without broader facility permissions. Role-based access controls automate these workflows, granting privileges tied to job functions and automatically expiring credentials when assignments end.
Tailored security services for hospitality and property development
Hospitality and property development sectors balance rigorous security with guest experience, requiring solutions that protect without creating friction. Concierge-style guarding exemplifies this balance: security personnel trained in customer service greet visitors warmly whilst verifying identities and monitoring for suspicious behaviours. Their dual role enhances safety perceptions amongst guests who view their presence as attentive service rather than intrusive surveillance.
CCTV systems integrate AI-driven video analytics that detect anomalies in real time. Machine learning algorithms trained on normal activity patterns flag deviations like unattended luggage in lobbies, individuals entering restricted floors, or crowds forming unexpectedly. These systems reduce false alerts by learning environmental baselines, distinguishing genuine threats from routine variations like housekeeping carts left temporarily in corridors.
Access control optimisation serves diverse user populations:
- Guest room locks using mobile credentials eliminate physical key cards vulnerable to cloning
- Biometric authentication for staff accessing back-of-house areas and storage facilities
- Visitor management systems capturing identification and issuing time-limited access badges
- Integration with property management platforms automatically updating permissions based on reservation status
Physical and cyber security convergence creates unified visibility across previously siloed systems. Integration platforms connect access controllers, video management software, intrusion detection panels, and IT security tools, feeding events into centralised SIEM platforms. Analysts correlate physical access attempts with network login failures, identifying credential theft or social engineering attacks. This convergence enables holistic threat detection impossible when systems operate independently.
Balancing security rigour with hospitality ensures safety without compromising guest comfort, transforming protection from necessary inconvenience into valued service differentiator.
Property development projects introduce temporary security challenges during construction phases. Sites require perimeter protection preventing theft of materials and equipment, yet access needs fluctuate as subcontractors rotate through projects. Mobile surveillance units with solar power and cellular connectivity provide flexible coverage, repositioning as construction progresses. Temporary access control systems issue contractor credentials tied to specific work phases, automatically expiring when assignments complete.
Pro Tip: Deploy AI-driven analytics identifying unusual patterns like repeated failed access attempts or individuals tailgating through secure doors, enabling proactive intervention before incidents escalate.
Smart building integration extends security beyond traditional concerns. IoT sensors monitoring environmental conditions detect anomalies indicating equipment failures or sabotage, whilst occupancy analytics optimise patrol routes and camera positioning. Building management systems integrate with security platforms, automatically locking zones during fire alarms or unlocking emergency exits when intrusion sensors trigger.

Core methodologies and frameworks underpinning security services
Foundational security methodologies guide effective service design across sectors, providing structured approaches that address diverse threats systematically. Understanding these principles enables IT managers to evaluate vendor proposals and ensure comprehensive coverage.
-
Defence-in-depth creates layered security zones that force attackers through multiple barriers, increasing detection likelihood and slowing progression. Outer layers include perimeter fencing and access controls, intermediate layers deploy network segmentation and intrusion detection, whilst inner layers protect critical assets with encryption and privileged access management. Each layer operates independently, ensuring single point failures do not compromise entire systems.
-
Crime Prevention Through Environmental Design applies architectural and landscaping principles that naturally discourage criminal activity. CPTED strategies include maximising natural surveillance through window placement and lighting, clearly defining public versus private spaces using landscaping and signage, and maintaining properties to signal active management. These passive measures complement active security controls, creating environments where suspicious behaviours become immediately apparent.
-
IT-physical convergence unifies previously separate security domains through integrated platforms and shared analytics. SIEM tools correlate events from access control systems, video surveillance, network firewalls, and endpoint protection, identifying sophisticated attacks exploiting both physical and cyber vectors. Converged operations centres staff analysts trained in both domains, eliminating coordination delays when incidents span multiple systems.
| Methodology | Primary focus | Key benefits | Typical application |
|---|---|---|---|
| Defence-in-depth | Layered barriers across zones | Redundancy, attack delay, multiple detection points | Manufacturing facilities, data centres, critical infrastructure |
| CPTED | Environmental design principles | Natural surveillance, reduced opportunity, passive deterrence | Property development, hospitality venues, educational campuses |
| IT-physical convergence | Unified security operations | Holistic visibility, faster correlation, coordinated response | Enterprise facilities, logistics hubs, mixed-use developments |
Defence-in-depth implementation requires careful zone definition. Perimeter fencing with intrusion detection forms the outermost layer, alerting security operations when breaches occur. Biometric mantraps at building entries verify identities before granting access to interior spaces. Within facilities, network segmentation isolates operational technology from administrative systems, whilst endpoint protection prevents malware execution on individual devices. This progression ensures attackers face escalating challenges at each stage.
CPTED principles influence architectural decisions during design phases. Eliminating hiding spots near entries through strategic landscaping, installing lighting that illuminates approaches without creating glare, and positioning reception desks with clear sightlines to entrances all enhance natural surveillance. Property developers incorporating these principles reduce security staffing requirements whilst improving safety perceptions amongst occupants.
Pro Tip: Integrate physical access control systems with IT network authentication, triggering security reviews when employees badge into facilities but do not log into networks, indicating potential credential compromise.
Framework adoption provides structure for continuous improvement. NIST Cybersecurity Framework’s five functions guide organisations through maturity progression: identifying assets and risks, protecting through appropriate safeguards, detecting anomalies and events, responding to confirmed incidents, and recovering normal operations. Regular assessments measure progress against framework categories, highlighting gaps requiring investment.
Risk-based prioritisation focuses resources on threats with highest potential impact. Vulnerability assessments identify weaknesses in current controls, threat modelling evaluates likelihood of exploitation, and business impact analysis quantifies potential losses. This data-driven approach justifies security investments to executive stakeholders, demonstrating return on investment through reduced incident frequency and severity.
Explore tailored security solutions with Re-Solution
Implementing the security strategies outlined requires expertise spanning physical controls, network architecture, and compliance frameworks. Re-Solution delivers bespoke security service packages addressing the specific challenges facing education, manufacturing, hospitality, and logistics sectors. Our approach integrates network security fundamentals with physical protection measures, creating unified defence architectures aligned to industry standards.
As a trusted Cisco partner with over 35 years of experience, we provide managed IT and security services that simplify complex infrastructure challenges. Our Security Operations Centre delivers continuous monitoring, threat intelligence, and incident response, addressing staffing limitations that prevent many organisations from maintaining in-house capabilities. Whether you require comprehensive security assessments, framework implementation guidance, or ongoing managed services, our team translates technical complexity into practical solutions supporting your operational objectives. Explore our detailed security services guide to discover how tailored approaches protect your critical infrastructure whilst enabling business growth.
Frequently asked questions about security services
How do MSSPs support educational institutions with limited cybersecurity staff?
Managed Security Service Providers deploy Security Operations Centre analysts who monitor school networks continuously, investigating alerts and responding to incidents without requiring in-house expertise. They provide threat intelligence specific to education sector attacks, vulnerability assessments, and compliance reporting that satisfy auditors whilst freeing internal IT staff to focus on instructional technology support.
What are best practices for integrating physical and cyber security in manufacturing?
Integration begins with converged platforms that correlate access control events, video surveillance, and network security alerts through SIEM tools. Implement OT/IT segmentation following the Purdue Model, deploy passive monitoring on industrial networks, and train security personnel in both physical and cyber threat indicators. Regular tabletop exercises testing coordinated incident response across manufacturing security teams ensure effective collaboration during actual events.
How can AI improve security services in hospitality?
AI-driven video analytics detect behavioural anomalies like loitering, tailgating, or unattended objects without human monitoring, reducing false alerts through learned baselines. Predictive analytics identify patterns indicating potential threats, such as repeated failed access attempts or unusual movement patterns. Machine learning optimises patrol routes based on historical incident data, focusing security resources on highest-risk areas and times.
What frameworks ensure compliance and risk management in different sectors?
NIST Cybersecurity Framework provides sector-agnostic structure applicable across industries, whilst specific regulations like FERPA for education or GDPR for hospitality data handling impose additional requirements. ISO 27001 offers certification demonstrating systematic information security management, and industry groups publish sector-specific guidance. Framework selection should align with regulatory obligations, customer expectations, and organisational risk tolerance.
How do you balance security rigour with operational efficiency?
Risk-based approaches focus stringent controls on high-value assets whilst applying proportionate measures elsewhere, avoiding universal restrictions that impede productivity. User-friendly technologies like mobile credentials and biometric authentication enhance security whilst reducing friction compared to traditional methods. Regular stakeholder consultation ensures security measures support rather than obstruct business processes, with continuous refinement based on operational feedback.
What role do physical security guards play in modern integrated systems?
Security personnel provide human judgement that technology cannot replicate, responding to ambiguous situations, verifying identities beyond automated systems, and deterring opportunistic threats through visible presence. They serve as first responders during incidents, coordinate with emergency services, and provide customer service in hospitality contexts. Integration with electronic systems enhances their effectiveness through real-time alerts and centralised communication platforms.
Recommended
- Security Services Explained: Essential Guide 2025 | Re-Solution
- Manufacturer’s Layered Security Approach | Re-Solution Experts
- Security in Manufacturing: Protect Facilities | Re-Solution
- Cybersecurity for Manufacturing: Why It Matters | Re-Solution
- Cybersecurity & Privacy – devPulse




