TL;DR:
- Traditional perimeter security and firewalls are insufficient for modern, dynamic networks.
- A secure network architecture applies layered principles like segmentation, Zero Trust, and continuous monitoring.
- Sector-specific approaches adapt these principles for manufacturing and educational environments, addressing unique risks.
Many IT leaders assume that a firewall at the perimeter and a few VLANs constitute a secure network. That assumption is costly. 40% of organisations experienced incidents due to inadequate network security, and the majority of those incidents exploited gaps that firewalls alone cannot address. Secure network architecture is a discipline that spans segmentation, identity, policy enforcement, and continuous monitoring. For IT managers in education and manufacturing, where compliance obligations and operational continuity are non-negotiable, understanding this discipline is not optional. This guide provides a structured, practical framework for building or improving your network security posture.
Table of Contents
- What is secure network architecture?
- Core components and methodologies
- Sector-specific approaches: manufacturing and education
- Modern challenges, emerging practices, and misconceptions
- Expert perspective: what most network architecture guides miss
- Practical next steps: move towards a secure network architecture
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Layered security essential | Relying solely on perimeter defences leaves critical gaps—segmentation and zero trust principles are vital. |
| Sector guides exist | Manufacturing and education benefit from industry-standard frameworks tailored to their compliance needs. |
| Migration is a journey | Practical progress comes from phased upgrades, beginning with proper asset segmentation and monitoring. |
| Misconceptions persist | Segmentation remains necessary, and zero trust is an architectural approach—not a product in itself. |
What is secure network architecture?
Secure network architecture is not a single product or configuration. It is a structured design philosophy that integrates multiple security principles across every layer of your network. As Forescout defines it, secure network architecture is a structured design integrating principles like defence-in-depth, segmentation, and zero trust to protect systems, data, and users at every layer.
The traditional perimeter model, where a firewall guards the boundary and everything inside is trusted, no longer reflects how networks operate. Users connect remotely. Devices span multiple sites. Cloud services sit outside any defined perimeter. Treating the internal network as a trusted zone creates a single point of failure.
Modern secure architecture replaces that assumption with a set of principles that apply consistently, regardless of where a user or device connects from. Understanding the secure network architecture basics helps clarify why this shift matters practically.
The core principles include:
- Defence-in-depth: Multiple overlapping security controls so that no single failure exposes the entire network.
- Segmentation: Dividing the network into zones with controlled communication paths, limiting lateral movement if a breach occurs.
- Zero Trust: Verifying every access request continuously, regardless of source location.
- Least-privilege access: Granting users and devices only the permissions they need for specific tasks.
- Visibility and monitoring: Continuous logging and analysis of network traffic to detect anomalies early.
- Compliance alignment: Designing controls to satisfy regulatory requirements from the outset, not as an afterthought.
Secure architecture is not a state you achieve once. It is an ongoing operational discipline that must evolve alongside your threat landscape and compliance obligations.
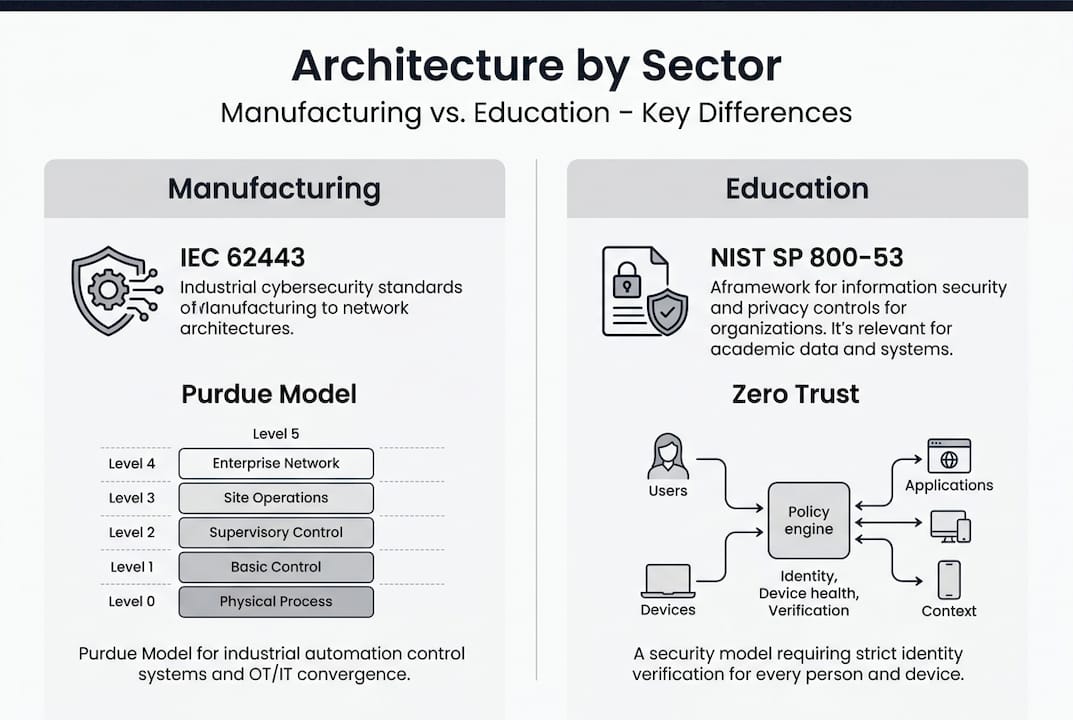
For manufacturing and education environments, regulatory requirements add urgency. Standards such as IEC 62443 for industrial networks and NIST SP 800-53 for information systems set specific expectations for access control, monitoring, and incident response. Reviewing network security best practices alongside these standards helps organisations map their controls to compliance requirements systematically. The NIST Zero Trust guidance provides a high-level reference for organisations beginning this journey.
Core components and methodologies
With the fundamentals clear, let us explore the technical components and frameworks behind a secure architecture.
A Zero Trust Architecture (ZTA) operates through two distinct functional elements. The Policy Decision Point (PDP) evaluates access requests against defined policies, considering identity, device posture, location, and context. The Policy Enforcement Point (PEP) acts on those decisions, allowing or blocking traffic in real time. As national standards confirm, core mechanics include the PDP, PEP, and use of least-privilege per-request access, separating the control plane from the data plane to reduce the blast radius of any compromise.
The key architectural components to implement are:
- Identity and access management (IAM): Authenticates every user and device before granting access.
- Microsegmentation: Divides the network into granular zones, restricting traffic between workloads even within the same VLAN.
- Network access control (NAC): Enforces policy at the point of connection, checking device compliance before admitting it to the network.
- Continuous monitoring and SIEM: Aggregates logs and alerts across all segments to detect and respond to threats in real time.
- Encrypted communications: Ensures data in transit is protected across all segments, including east-west traffic inside the network.
| Component | Primary function | Key benefit |
|---|---|---|
| PDP | Policy evaluation | Centralised decision logic |
| PEP | Policy enforcement | Consistent access control |
| Microsegmentation | Traffic isolation | Limits lateral movement |
| NAC | Device admission control | Blocks non-compliant devices |
| SIEM | Threat detection | Early incident identification |
NIST SP 1800-35 documents 19 ZTA builds using commercial technology, demonstrating that Zero Trust is practical and achievable across varied environments, not a theoretical ideal. Each build illustrates how organisations combine these components differently based on their existing infrastructure and risk profile.
Pro Tip: Before selecting technology, map your existing network zones and identify which assets carry the highest risk. Microsegmentation is most effective when applied to your most sensitive workloads first, rather than attempting a full network rollout simultaneously.

Exploring zero trust methodologies and reviewing zero trust benchmarks against your current posture gives you a practical starting point for prioritising implementation effort.
Sector-specific approaches: manufacturing and education
Next, let us see how these architectural principles play out differently in manufacturing versus educational environments.
Manufacturing networks face a distinctive challenge: operational technology (OT) systems, such as programmable logic controllers (PLCs) and SCADA platforms, were designed for reliability and availability, not security. The Purdue Model and IEC 62443 provide the foundational framework for manufacturing network segmentation, organising systems into hierarchical levels from field devices up to enterprise IT, with controlled interfaces between each level.
Manufacturing priorities:
- Isolate OT networks from corporate IT using demilitarised zones (DMZs).
- Maintain a full asset inventory of all connected devices, including legacy equipment.
- Apply IEC 62443 zone and conduit models to define and enforce communication paths.
- Use unidirectional gateways where data must flow from OT to IT without return traffic.
- Restrict remote access to OT systems through dedicated, monitored jump servers.
Educational institutions face a different risk profile. Open networks serving thousands of students, staff, and guests create broad attack surfaces. Bring-your-own-device (BYOD) policies, research systems, and administrative data all coexist on the same infrastructure.
Education priorities:
- Segment guest, student, staff, and administrative networks as distinct zones.
- Apply NIST SP 800-53 controls for access management and incident response.
- Implement ZTA for staff and administrative access to sensitive systems.
- Enforce NAC to validate device compliance before granting network access.
- Maintain visibility across all segments with centralised monitoring.
| Factor | Manufacturing | Education |
|---|---|---|
| Primary standard | IEC 62443, Purdue Model | NIST SP 800-53, ZTA |
| Key risk | OT/IT boundary exposure | BYOD and open access |
| Critical control | Zone and conduit segmentation | NAC and identity management |
| Monitoring focus | OT protocol anomalies | User behaviour and access patterns |
Pro Tip: In manufacturing, never assume that air-gapping OT systems is sufficient. Remote maintenance access and supply chain connections frequently bridge those gaps. Document every connection point and apply explicit policy controls to each one.
Reviewing sector-specific network designs and the modern Purdue model applications provides practical examples of how these frameworks are applied in live environments.
Modern challenges, emerging practices, and misconceptions
With sector strategies in mind, we can turn to the modern challenges, new practices, and persistent myths in network architecture.
Three forces are reshaping network security faster than most architectures can adapt: cloud adoption, remote access at scale, and the proliferation of IoT and OT devices. Each introduces connectivity patterns that traditional perimeter models cannot handle.
Cloud services sit outside your network boundary entirely. Remote workers connect from unmanaged environments. IoT sensors in manufacturing plants use protocols that security tools were not designed to inspect. Addressing these realities requires architectural changes, not just additional appliances.
The most persistent misconceptions include:
- “Segmentation is obsolete with Zero Trust.” Segmentation remains essential. ZTA governs access decisions, but segmentation limits the blast radius when those decisions are wrong or when a compromised credential is used.
- “Zero Trust is a product you can buy.” ZTA is an architectural principle, not a single platform. As security standards make clear, ZTA is not a product, segmentation is still required, and Purdue limitations must be addressed with overlays and additional controls.
- “A VPN is sufficient for remote access.” Traditional VPNs grant broad network access once authenticated. Zero Trust Network Access (ZTNA) replaces this with per-session, per-application access decisions based on current context.
The question is not whether your current architecture will be challenged by modern threats. It is whether your architecture will detect and contain that challenge before it becomes a breach.
Emerging practices include micro-DMZs, which create isolated zones for specific workloads or devices rather than broad network segments, and software-defined networking (SDN) overlays that apply Zero Trust policy across existing infrastructure without requiring a full hardware replacement.
For IoT environments, the priority is discovery and classification before policy. You cannot protect what you cannot see. Automated asset discovery tools integrated with NAC platforms provide the visibility needed to enforce policy consistently. Reviewing network security challenges and the NIST 19 ways for zero trust gives practical direction for addressing these gaps systematically.
Expert perspective: what most network architecture guides miss
Most guides focus on frameworks and technologies. Fewer address the operational reality that security architecture must coexist with the people and processes already running your organisation.
The most common failure we observe is not a technical one. Organisations invest in the right components but implement them in a single large migration that disrupts operations, overwhelms IT teams, and produces a brittle result. A phased, outcome-driven approach consistently outperforms the so-called big-bang deployment. As NIST SP 1800-35 demonstrates, balancing security with operational needs and adopting phased, benchmark-driven migration produces sustainable, measurable results.
Start with a pilot segment. Prove the model. Measure the outcome. Then extend. This approach builds institutional confidence alongside technical capability. It also allows compliance evidence to accumulate incrementally, which auditors and regulators respond to positively.
The other overlooked reality is that security and IT/OT innovation must move together. When operational teams bypass security controls because they impede productivity, the architecture fails regardless of its theoretical soundness. Reviewing practical build strategies with your operational stakeholders, not just your security team, is the step most organisations skip.
Practical next steps: move towards a secure network architecture
Understanding the principles is the starting point. Translating them into a working architecture requires structured assessment, clear prioritisation, and the right implementation support.
Re-Solution works with IT managers in education and manufacturing to assess existing network posture, identify compliance gaps, and design phased implementation plans that balance security with operational continuity. With over 35 years of Cisco expertise, our team supports everything from initial network surveys through to managed Network as a Service support for ongoing security operations. Whether you are starting with a segmentation pilot or planning a full Zero Trust migration, our IT infrastructure explained resources and specialist consultants provide a clear, practical path forward. Contact Re-Solution to arrange an infrastructure assessment and take the first concrete step towards a resilient, compliant network.
Frequently asked questions
What are the minimum components of a secure network architecture?
A secure network architecture requires segmentation, policy enforcement, continuous monitoring, and least-privilege access using components like PDPs and PEPs. These elements work together to control access and contain threats across every network zone.
How does Zero Trust differ from perimeter security?
Zero Trust continuously verifies every access request regardless of the user’s location, replacing the perimeter model’s assumption that internal traffic is inherently trustworthy. This removes the single point of failure that perimeter security creates.
Should educational institutions implement Zero Trust architecture?
Yes. NIST SP 800-53 and ZTA mandates are increasingly expected for educational networks, particularly where administrative and student systems share infrastructure. The open access nature of education environments makes continuous verification essential.
Is the Purdue Model still relevant for manufacturing?
Yes, but it requires modernisation. Modern manufacturing applies micro-DMZs and Zero Trust overlays on top of the Purdue hierarchy to address remote access, cloud connectivity, and supply chain integration that the original model did not anticipate.
Recommended
- How to build secure network architectures for lasting protection
- Secure network design: proven examples for robust protection
- Understanding Cloud Networking: Expert Guide | Re-Solution
- Understanding Cloud Networking: Expert Guide | Re-Solution




