Traditional perimeter security is no longer sufficient for protecting modern networks, and NIST SP 1800-35 makes this clear. Schools hold sensitive student records, manufacturers run critical industrial systems, and both sectors face mounting ransomware threats and regulatory pressure. The old model of trusting everything inside the firewall is a liability. This guide gives IT managers and decision-makers in education and manufacturing a practical blueprint for building secure network architectures that hold up under real-world conditions.
Table of Contents
- Why secure network architecture matters now
- Core principles of secure network architecture
- Key components of a secure network architecture
- Step-by-step framework for implementation
- Special considerations for educational and manufacturing environments
- Building resilience and continuous improvement
- Take your network security to the next level
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Zero Trust as foundation | Adopt Zero Trust to move beyond perimeter defences and require constant verification of all users and devices. |
| Segmentation stops attacks | Effective network segmentation contains threats, limiting risk to critical assets and data. |
| Continuous improvement | Regular monitoring, audits, and training are essential to adapt and stay resilient against evolving threats. |
| Education and ICS focus | Tailor your architecture for sector needs—protect student data in schools and legacy systems in manufacturing. |
| Actionable roadmap | Follow a phased plan: assess, prioritise, implement, verify, and iterate for sustainable security and compliance. |
Why secure network architecture matters now
Cyberattacks on schools and manufacturers have surged in recent years. Ransomware gangs specifically target these sectors because they hold valuable data and often run legacy infrastructure that is harder to patch quickly. The financial and reputational cost of a breach is significant, and regulatory fines add further pressure.
Compliance requirements are tightening. Schools in the UK and US must meet standards such as CIPA and FERPA, while manufacturers face IEC 62443 for industrial control systems. Security for educational environments confirms that network segmentation and access controls are essential for CIPA and FERPA compliance and to mitigate ransomware risk.
The core problem with perimeter-based thinking is the assumption that internal traffic is safe. Once an attacker is inside, they move laterally with ease. Effective managing school network access and applying network security best practices are now baseline expectations, not optional extras.
The ‘trust but verify’ model is obsolete. Continuous verification of every user, device, and connection is the new standard for any organisation serious about security.
Key risks driving this shift include:
- Ransomware targeting student and operational data
- Insider threats and compromised credentials
- Unpatched legacy devices on shared networks
- Regulatory fines for non-compliance with data protection standards
- Supply chain attacks via third-party vendor access
With the urgency established, it is crucial to understand which models actually deliver security in today’s landscape.
Core principles of secure network architecture
Modern secure network architecture rests on a handful of well-defined principles. Understanding these gives you a framework for every decision that follows.
Zero Trust Architecture (ZTA) is the most significant shift in network security thinking. Zero Trust assumes no implicit trust and requires continuous verification for every user, device, and resource, regardless of location. Our Zero Trust methodology page explains how this applies in practice for distributed organisations.
Microsegmentation goes further than traditional network segmentation. Where segmentation creates broad zones, microsegmentation enforces granular policies at the workload level. An attacker who breaches one segment cannot automatically reach another.
Software-Defined Networking (SDN) enables dynamic policy enforcement across the network. Rather than relying on static hardware configurations, SDN for network security allows policies to adapt in real time as threats evolve.

CIS Controls v8 emphasise asset inventory and ongoing vulnerability management as critical foundations. Without knowing what is on your network, you cannot protect it.
| Approach | Scope | Key benefit |
|---|---|---|
| Perimeter security | Network edge only | Simple to deploy |
| Network segmentation | Broad zones | Limits lateral movement |
| Microsegmentation | Workload level | Granular control |
| Zero Trust Architecture | Every user and device | Continuous verification |
| SDN-based policy | Dynamic, network-wide | Adaptive enforcement |
Pro Tip: Start with asset discovery before deploying any new security controls. You cannot segment or protect what you have not catalogued. A simple spreadsheet audit is a valid first step.
Key principles to apply from day one:
- Least privilege access for all users and systems
- Continuous authentication rather than one-time login
- Encryption of data in transit and at rest
- Visibility across all network segments via centralised logging
Equipped with principles, let us explore the real building blocks: key architectural components and practical examples.
Key components of a secure network architecture
Principles only become useful when translated into specific technologies and configurations. Here are the essential components for education and manufacturing environments.
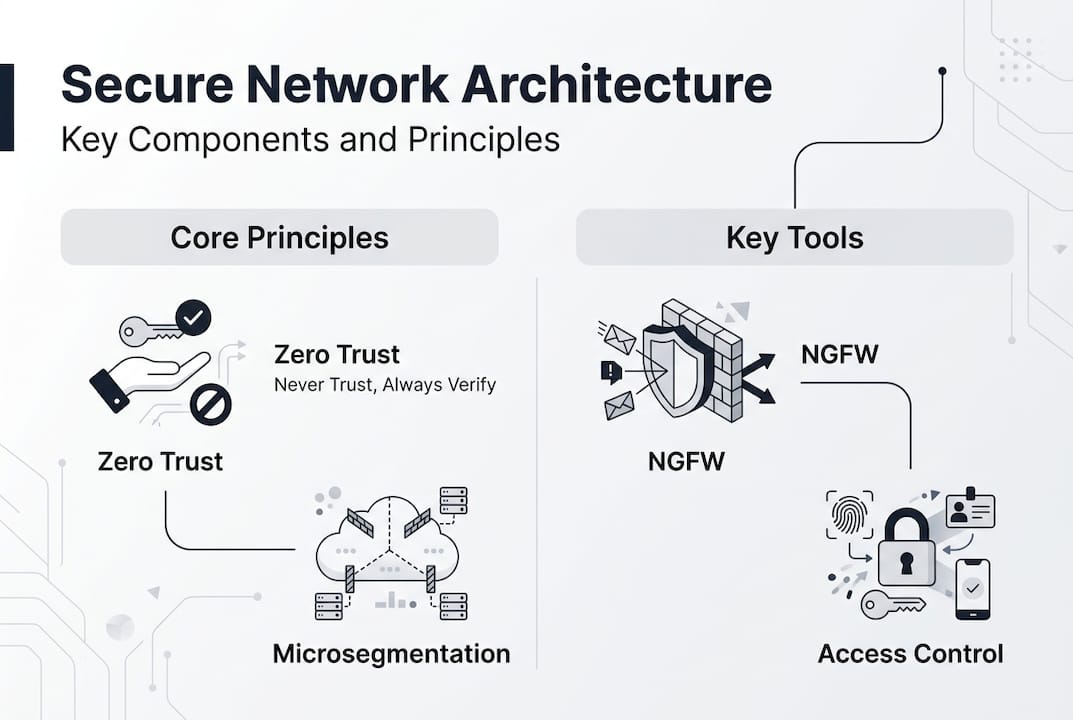
Next-generation firewalls (NGFWs) inspect traffic at the application layer, not just port and protocol. They block sophisticated threats that traditional firewalls miss. Our guidance on firewalls and segmentation covers how to position these effectively.
Access control enforces who can reach what. Role-based access control (RBAC) assigns permissions based on job function, not individual preference. Managing access policies with tools like Cisco Meraki simplifies this at scale. Implementing access controls correctly is one of the highest-impact steps you can take.
Network segmentation using VLANs and subnets creates logical boundaries between departments, systems, and user groups. A student VLAN should never have direct access to administrative systems.
Monitoring and threat detection via Network Detection and Response (NDR) tools gives you visibility into anomalous behaviour. The Australian Cyber Security Centre prioritises patching internet-facing devices, multi-factor authentication (MFA), egress filtering, and NDR as core network defences.
Patch management is unglamorous but critical. Unpatched systems are the most common entry point for attackers. You can check whether your current approach is working by verifying network security against a structured checklist.
| Component | Education use case | Manufacturing use case |
|---|---|---|
| NGFW | Filter student internet traffic | Protect OT/IT boundary |
| RBAC | Separate staff and student access | Limit ICS operator permissions |
| VLANs | Isolate BYOD devices | Separate production and office networks |
| NDR | Detect unusual login patterns | Monitor IIoT device behaviour |
| Patch management | Update classroom devices | Patch SCADA systems safely |
Pro Tip: For manufacturing environments, schedule patches during planned maintenance windows to avoid disrupting production. Coordinate with operations teams before any change to industrial systems.
With components in hand, it is critical to walk through how they are combined, step by step, for practical deployment.
Step-by-step framework for implementation
Building a secure network architecture is a phased process. Trying to do everything at once leads to gaps and misconfigurations. Follow this sequence:
- Assess your assets and risks. Catalogue every device, system, and data flow. Identify your highest-risk zones and existing controls. CIS Controls v8 asset inventory guidance is a practical starting point.
- Prioritise network zones. Identify which systems hold the most sensitive data or control critical processes. These get the strongest controls first.
- Select your technology stack. Choose firewalls, SDN platforms, NDR tools, and MFA solutions appropriate to your scale and budget. Our network planning guide helps structure these decisions.
- Implement and configure each layer. Deploy segmentation, access controls, and monitoring in stages. Test each layer before moving to the next.
- Validate with audits and penetration testing. Do not assume configuration equals protection. Regular testing reveals gaps that documentation misses. Review security best practices to benchmark your posture.
- Iterate continuously. Threats evolve. Your architecture must too. NIST SP 1800-35 demonstrates 19 real-world Zero Trust builds with 24 collaborators, proving that no two deployments are identical.
Key inputs for each phase:
- Asset register and network diagrams
- Risk assessment aligned to your compliance obligations
- Stakeholder sign-off on segmentation boundaries
- Defined incident response procedures before go-live
Finally, let us address the unique challenges and opportunities for educational institutions and manufacturers.
Special considerations for educational and manufacturing environments
Both sectors share common security challenges but face distinct operational realities that shape how architecture decisions are made.
Education-specific considerations:
- BYOD (bring your own device) policies introduce unmanaged endpoints onto school networks. Isolate these on dedicated VLANs with restricted access.
- Safeguarding student data under FERPA and UK GDPR requires strict access logging and data minimisation.
- Ransomware defence depends heavily on access management in schools and regular offline backups.
- Content filtering must meet CIPA requirements without blocking legitimate educational resources.
Manufacturing-specific considerations:
- Industrial Control Systems (ICS) and Operational Technology (OT) networks must be isolated from corporate IT using the Purdue model or equivalent segmentation.
- Legacy systems often cannot be patched. Compensating controls such as network isolation and application whitelisting are essential.
- IIoT (Industrial Internet of Things) devices expand the attack surface significantly. Each device is a potential entry point.
- IEC 62443 provides a structured framework for securing industrial automation and control systems.
SDN-based architectures offer particular value here. Research on SDN-based security frameworks shows the SecuNet-4D framework achieves 95% threat detection and 98.5% attack prevention, demonstrating the measurable impact of dynamic policy enforcement.
For manufacturers running legacy OT systems, isolation is more achievable than patching. A well-configured air gap or firewall boundary buys time while longer-term modernisation is planned.
For both sectors, rapid incident response planning is non-negotiable. Knowing exactly which systems to isolate and who to contact when an attack occurs reduces recovery time dramatically. Reviewing cloud security practices is also worthwhile as hybrid environments become more common.
After examining sector-specific practices, it is important to summarise how these strategies position your network for long-term resilience.
Building resilience and continuous improvement
A secure network architecture is not a one-time project. It is an ongoing operational commitment. The threat landscape shifts constantly, and your defences must keep pace.
Continuous monitoring and adjustment are essential for effective network defence. This means deploying SIEM (Security Information and Event Management) tools, reviewing logs regularly, and acting on alerts rather than archiving them.
Key practices for sustained resilience:
- Schedule quarterly network audits to identify configuration drift and new vulnerabilities
- Run annual penetration tests to validate segmentation and access controls
- Deliver regular user awareness training, as phishing remains the most common initial access vector
- Maintain and test an incident response plan at least twice per year
- Review compliance obligations annually as regulations evolve
Pro Tip: Assign a named owner for each network segment. When a security incident occurs, knowing exactly who is responsible for each zone accelerates response time significantly.
Ongoing monitoring tools give you the visibility needed to catch misconfigurations before attackers do. Pair this with a culture of security awareness across your organisation, and you create multiple layers of human and technical defence.
Building adaptable infrastructure means designing for change from the outset. Use SDN where possible to allow policy updates without hardware reconfiguration. Document every change and maintain version-controlled network diagrams.
Take your network security to the next level
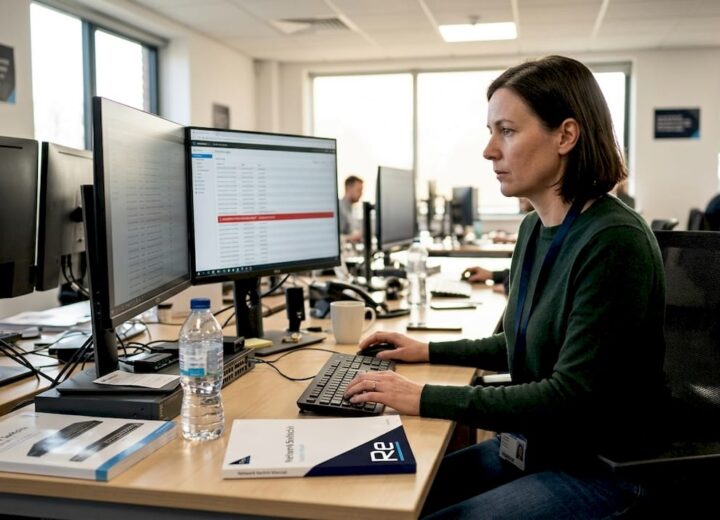
Building a secure network architecture requires the right expertise, tools, and ongoing commitment. Re-Solution has supported educational institutions and manufacturers for over 35 years as a trusted Cisco partner, helping organisations modernise their infrastructure, achieve compliance, and reduce risk.
Whether you need a structured network audit to identify gaps, guidance on Zero Trust adoption, or a fully managed approach through our network-as-a-service offering, we can tailor a solution to your environment. Explore our network solutions overview to understand the full range of support available. Get in touch with our team to discuss your specific requirements and take the next step towards a more resilient network.
Frequently asked questions
What is Zero Trust and why is it important for secure networks?
Zero Trust is a security model that assumes no implicit trust and requires continuous verification of every user and device, making it highly effective against modern threats including insider attacks and compromised credentials.
How does network segmentation prevent cyber attacks?
Segmentation creates secure boundaries using virtual networks, subnets, and firewalls, isolating high-risk workloads and limiting how far an attacker can move once inside the network.
Which security measures are essential for compliance in schools?
Firewalls, network segmentation, access controls, and content filtering are the core requirements for CIPA and FERPA compliance, alongside regular audits and staff training.
How can manufacturers secure industrial control systems?
Manufacturers should isolate ICS and OT networks using the Purdue model, apply IEC 62443 standards, and use SDN and microsegmentation to manage legacy and IIoT device risks.
What are the first steps in implementing a secure network architecture?
Begin with a full asset inventory and risk assessment, then prioritise critical zones for segmentation, following CIS Controls v8 guidance on asset management and vulnerability prioritisation.
Recommended
- How to Build a Secure Network: Step-by-Step | Re-Solution
- How to Build a Secure Network: Step-by-Step | Re-Solution
- Network Security Best Practices Guide | Re-Solution
- Network Security Best Practices Guide | Re-Solution
- Traditional Security vs AI-Powered Protection | Singleclic