TL;DR:
- Network breaches are a routine operational challenge affecting sectors like education, manufacturing, and hospitality, with minimal containment time increasing their impact. An investment in security controls based on enterprise risk management provides targeted, measurable risk reduction aligned with business objectives. Continuous reassessment and expert guidance are essential for maintaining effective, integrated network security that prevents costly disruptions and reputational damage.
Network breaches are not a distant possibility for enterprises in education, manufacturing, and hospitality. They are a routine operational challenge. Nearly nine in ten higher education institutions in the UK reported experiencing breaches or attacks in the last 12 months. That figure alone should recalibrate how IT leaders think about their security budgets. This guide explains how to frame network security investment not as a cost centre, but as a direct contributor to enterprise resilience, operational continuity, and long-term business value.
Table of Contents
- The real cost of network breaches in enterprise sectors
- Aligning network security investment with enterprise objectives
- Selecting the most effective network security controls
- Building a business case for network security investments
- What most IT leaders overlook about network security investments
- Strengthen your network with expert guidance
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Breaches remain common | Major incidents still affect most enterprises in education and related sectors. |
| Risk-driven investment wins | Network security spend is most effective when tied to enterprise objectives and clear risk priorities. |
| Controls should match risk | Choose controls that address your top risks for maximum business impact. |
| Actionable business case | Connect controls to specific outcomes and costs to secure stakeholder buy-in. |
| Expert support accelerates success | The right external guidance and audits can raise your network security posture. |
The real cost of network breaches in enterprise sectors
Having highlighted the breach frequency, we can now detail why these incidents have such widespread consequences for enterprises.
Network breaches rarely stay contained within the IT department. When a manufacturing plant loses access to its operational systems, production halts. When a hotel’s guest-facing network is compromised, trust evaporates quickly. When a university loses control of sensitive research data, the reputational fallout can last years. Understanding this wider blast radius is essential for any IT leader building a case for network security investment.
The statistics bear this out. Over one in four further and higher education institutions reported experiencing breaches or attacks at least weekly, and 49% of impacted organisations suffered negative outcomes. These are not minor nuisances. They represent real harm to students, staff, institutional data, and operational continuity.
“The question is no longer whether your sector will be targeted. It is how prepared your organisation is to limit the damage when an incident occurs.”
The following table summarises the typical business impact of network breaches across the three sectors most relevant to this guide:
| Sector | Common attack vectors | Primary negative outcomes |
|---|---|---|
| Education | Phishing, ransomware, credential theft | Data loss, service disruption, regulatory exposure |
| Manufacturing | OT/IT boundary attacks, insider threats | Production downtime, IP theft, safety risks |
| Hospitality | Guest Wi-Fi exploitation, POS attacks | Payment data breaches, reputational damage, fines |
Beyond the immediate disruption, organisations also face secondary consequences that compound over time:
- Regulatory fines under UK GDPR and sector-specific frameworks, which can reach millions of pounds for serious data breaches
- Increased cyber insurance premiums, as insurers tighten eligibility criteria based on incident history and control maturity
- Loss of contracts or funding, particularly relevant for education institutions that rely on research grants or public sector procurement
- Staff and student attrition, as confidence in institutional security erodes following public breaches
- Extended remediation costs, including forensic investigation, system rebuilding, and third-party incident response services
Staying informed on current threats is a valuable discipline. Reviewing weekly attack summaries gives IT teams a practical picture of live threat activity across sectors, which can directly inform risk prioritisation decisions.
The key takeaway here is that containment speed and response quality determine how severe the downstream impact becomes. This is why the controls you select, and the investment behind them, matter far more than simply having a firewall in place.
Aligning network security investment with enterprise objectives
To translate risk into practical controls, let’s look at how risk management frameworks inform investment decisions.
Many enterprises still approach security spending reactively. A breach occurs or an audit finding surfaces, and budget is released to address the specific gap. This cycle is costly and leaves organisations perpetually one step behind the threat landscape. A risk-based investment model changes that dynamic fundamentally.
According to NIST IR 8286B-upd1, network security spend should be justified using enterprise risk management methods: identify risks, prioritise them against enterprise objectives, and select cost-effective risk responses and controls. This approach connects every security investment directly to a business outcome, making it far easier to justify to finance and executive stakeholders.

The following comparison shows how traditional spending differs from a risk-driven approach:
| Approach | Basis for investment | Outcome |
|---|---|---|
| Traditional (reactive) | Incidents, audits, vendor recommendations | Fragmented coverage, budget waste, gaps remain |
| Risk-driven (proactive) | Business objectives, risk register, threat landscape | Targeted controls, measurable risk reduction, clear ROI |
Adopting a risk-driven approach involves a structured sequence of steps. This is not complicated, but it does require discipline and cross-functional input:
- Identify enterprise assets and dependencies. Map which systems, data, and processes are critical to delivering your core mission. In a university, that might include student records systems and research networks. In a hotel group, it includes reservation platforms and payment infrastructure.
- Assess threats and vulnerabilities against each asset. Use current threat intelligence and internal audit findings to understand where exposure is highest. Reviewing network security best practices provides a useful reference point for this stage.
- Prioritise risks by likelihood and business impact. Not all risks are equal. A ransomware attack on a manufacturing OT network carries a very different cost from a phishing attempt on a non-critical mailbox.
- Evaluate cost-effective risk responses. For each prioritised risk, determine whether the best response is a technical control, a policy change, a transfer mechanism such as insurance, or risk acceptance.
- Allocate budget according to risk priority. This ensures the highest-impact controls receive funding first, rather than budget flowing to familiar or vendor-pushed tools.
This approach also provides a structured foundation for infrastructure strategy planning, ensuring that security investments align with broader technology roadmaps rather than sitting in isolation.
A well-structured security investment programme, grounded in enterprise risk management, typically reduces wasted spend significantly. When controls are selected based on defined risks rather than gut instinct, organisations avoid purchasing tools that duplicate coverage or address threats that are not materially relevant to their environment. For a secure network architecture that supports long-term resilience, this disciplined approach is the most reliable starting point.
Selecting the most effective network security controls
With an investment strategy in place, IT leaders must then select controls that tangibly reduce exposure and loss.
Control selection is where many organisations stumble. The market is saturated with security products, each claiming to be essential. Without a clear risk baseline, procurement decisions often favour the loudest vendors rather than the most relevant controls. The evidence from the education sector specifically supports a focus on containment-focused controls such as segmentation, access governance, and rapid detection to reduce negative incident outcomes.
These four control categories consistently deliver measurable risk reduction across education, manufacturing, and hospitality environments:
- Network segmentation. Dividing the network into isolated zones prevents lateral movement during an incident. If an attacker compromises a guest Wi-Fi segment in a hotel, segmentation stops them from reaching the payment systems or back-office network. In manufacturing, it keeps OT (operational technology) environments separate from corporate IT systems.
- Access governance and NAC (Network Access Control). Controlling who and what can connect to the network is foundational. This includes device authentication, role-based access policies, and continuous verification. In education environments with thousands of students and staff devices, NAC is particularly important.
- Monitoring and detection. Real-time visibility across the network enables faster identification of anomalous behaviour. This includes SIEM (Security Information and Event Management) tools, intrusion detection systems, and log aggregation. The faster an incident is identified, the smaller the blast radius.
- Incident response pathways. Having pre-defined response procedures for common incident types means teams act quickly rather than improvising. Response time is directly correlated with the severity of negative outcomes.
Sector-specific nuances matter here. Education networks are highly diverse, with a mix of institutional devices, personal student devices, and research equipment. This requires flexible access governance that can apply different policies to different user and device classes. Manufacturing environments must address the convergence of OT and IT networks, often with legacy equipment that cannot support modern security agents. Hospitality networks prioritise guest experience, so controls must be transparent to end users while remaining robust against external threats.
The security controls guide and secure design examples are particularly useful references when mapping controls to your specific environment and risk profile.
Pro Tip: Before purchasing any security tool, map it explicitly to a risk identified in your risk register. If you cannot name the specific threat it addresses and the business asset it protects, the investment is unlikely to deliver measurable value.
Building a business case for network security investments
Once the right controls are identified, the last mile is convincing budget holders with a robust business case.
IT leaders consistently cite executive buy-in as one of the most significant barriers to progressing security investments. The disconnect typically arises because technical risk language does not translate naturally into business language. Closing that gap requires deliberate effort.
Building a credible business case starts with articulating risk in terms that resonate with finance directors and operational leaders. Rather than describing a vulnerability in technical terms, frame it as a probability of a specific business disruption with an estimated financial consequence. For example, a ransomware incident affecting a university’s student records system is not just a data protection concern. It represents potential regulatory fines under UK GDPR, a likely interruption to student services during a critical period such as enrolment or examinations, and potential reputational damage that influences future student recruitment.
NIST IR 8286B-upd1 notes that adding risk priorities and response information to a cybersecurity risk register supports enterprise risk register views and helps adjust risk strategy to ensure mission success. This connection between the security risk register and the broader enterprise risk register is precisely what gives security investments legitimacy at board level.
Follow these steps to structure a compelling business case:
- Quantify the risks you are addressing. Use breach frequency data, sector statistics, and internal incident history to establish a credible probability of harm. Reference the education sector figures in this guide as external benchmarks where appropriate.
- Map each proposed control to a specific risk. Show clearly how the investment reduces the likelihood or impact of the identified risk. Avoid vague claims about “improving security posture.”
- Calculate the cost of inaction. Estimate the potential financial impact of an unmitigated incident, including remediation costs, regulatory fines, and operational disruption. Compare this against the cost of the proposed control.
- Present a prioritised investment roadmap. Rather than requesting a large budget in one tranche, demonstrate a phased approach that prioritises the highest-risk controls first. This builds confidence with budget holders and allows for iterative progress.
- Define success metrics. Identify how you will measure whether the investment has achieved its intended risk reduction. This could include mean time to detect, incident frequency, or audit compliance scores.
“Security investments that cannot be connected to specific business outcomes will always be vulnerable to budget cuts. The risk register is your most powerful tool for making those connections visible.”
Exploring a modern security strategy framework can also help IT leaders structure their thinking before entering budget discussions, ensuring the narrative is coherent from risk identification through to investment justification.
What most IT leaders overlook about network security investments
There is a persistent assumption in enterprise security that higher spend automatically produces better outcomes. The data does not support this. Organisations that invest heavily in point solutions without aligning them to a defined risk strategy often end up with overlapping tools, alert fatigue among security teams, and significant gaps in areas that were never properly assessed.
The single biggest mistake we observe is adopting controls because they are popular or because a peer organisation adopted them, rather than because they address a specific, documented risk. This is particularly common in sectors experiencing rapid digital transformation, where the pressure to appear modern can override the discipline of risk-led investment. Education institutions adopting cloud-native networking tools, for example, sometimes focus on connectivity features without fully evaluating the access governance implications.
Cross-sector lessons are increasingly relevant in 2026. Manufacturing organisations can learn from the access governance maturity of financial services. Hospitality businesses can draw on the guest-segmentation models pioneered in large enterprise campuses. Education institutions, despite having some of the most challenging network environments, are often ahead of hospitality peers in their adoption of Zero Trust network access (ZTNA) principles, precisely because their threat exposure has been higher for longer.
Integrated security solutions that combine connectivity, compliance, and access control within a coherent architecture deliver more consistent outcomes than collections of standalone tools. The integration piece is often undervalued during procurement, but it determines whether your controls function as a coordinated defence or as isolated components that attackers can route around.
The organisations that get this right share one characteristic: they treat security investment as a continuous business process, not a periodic procurement exercise. Risk landscapes change. Business models evolve. The controls that were sufficient two years ago may leave material gaps today.
Strengthen your network with expert guidance
For leaders ready to move beyond theory and drive real improvements, expert support accelerates results.
Re-Solution brings over 35 years of Cisco infrastructure expertise to enterprise network security across education, manufacturing, and hospitality. Whether you are building your first structured risk register, evaluating your current control coverage, or planning a phased network security upgrade, the right starting point is a clear picture of where you stand.
Our network access control guide is a practical resource for IT leaders evaluating access governance options, and our network audit services provide the independent visibility needed to identify gaps that internal reviews often miss. When you are ready to discuss your specific environment and objectives, speak to our experts to explore how a structured, risk-led approach can strengthen your network security investment.
Frequently asked questions
What are the top business risks if I neglect network security investment?
Neglecting network security exposes organisations to data loss, operational downtime, regulatory fines, and lasting reputational damage. Almost half of UK further and higher education institutions that identified a breach reported negative system outcomes.
How do I justify network security spending to non-technical executives?
Connect each investment to a specific business risk and the cost of the negative outcome it prevents, rather than describing it in technical terms. Risk registers linking controls to enterprise objectives are the most effective tool for making security investments credible at board level.
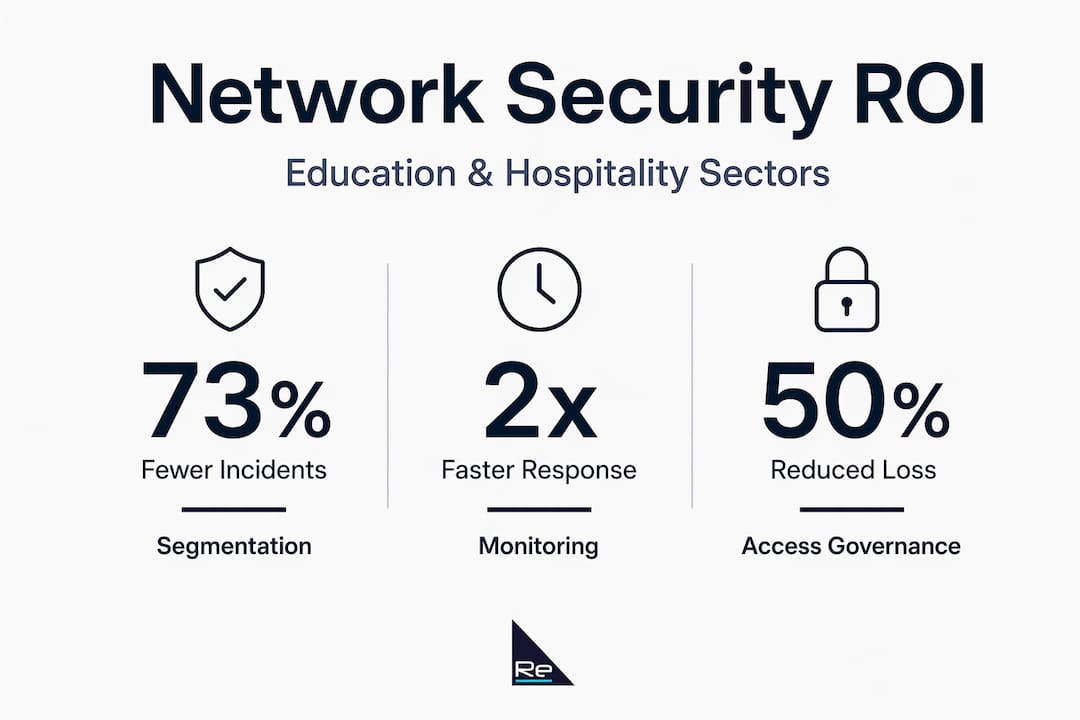
Which network security controls give the best ROI in education and hospitality?
Segmentation, access governance, and real-time monitoring consistently reduce incident impact across both sectors. Education sector evidence specifically supports containment-focused controls for effective incident response and minimising negative outcomes.
How often should our enterprise re-assess network security investments?
Risk posture and control effectiveness should be reviewed at least annually, and immediately following any significant infrastructure change, merger, or confirmed security incident.
Recommended
- Network Security Best Practices Guide | Re-Solution
- Network Security Best Practices Guide | Re-Solution
- Integrated security solutions: Boost connectivity and compliance
- Secure network design: proven examples for robust protection





