Managing network access is increasingly complex due to BYOD, IoT, and legacy systems. IT managers in educational institutions, manufacturing, and hospitality sectors face the challenge of securing diverse devices and users without disrupting operations. A structured network access policy workflow is essential for maintaining security and operational efficiency. This guide will walk you through problem understanding, preparation, execution, and verification steps to design and deploy effective network access policies tailored to your organisation’s unique environment.
Table of Contents
- Key takeaways
- Understanding the challenges with network access policies
- Preparing your network access policy workflow
- Executing network access policy workflows step by step
- Verifying and maintaining your network access policy workflow
- Enhance your network security with expert solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| NAC core method | Network Access Control is the primary methodology for enforcing access policies by validating device and user compliance before access is granted through authentication, authorisation, posture assessment, and remediation workflows. |
| Sector tailored workflows | Policy design should reflect sector needs such as education, manufacturing and hospitality to balance security with operational practicality. |
| Phased deployment advantage | Pilot programmes and staged rollouts help identify issues early and prevent widespread access disruption. |
| Legacy device compatibility | Prepare for devices that cannot support modern authentication by planning compatible approaches and prioritising monitoring over blocking. |
| Regular review and verification | Ongoing policy effectiveness requires regular reviews to verify posture, update controls and refine workflows. |
Understanding the challenges with network access policies
Securing network access requires more than installing firewalls and setting passwords. Network Access Control (NAC) is the primary methodology for implementing network access policies, enforcing device and user compliance before granting access via authentication, authorisation, posture assessment, and remediation workflows. Yet implementing NAC effectively presents significant challenges.
BYOD initiatives, IoT sensors, legacy systems, and operational technology devices complicate policy enforcement. Each device type brings unique authentication capabilities and security risks. A manufacturing plant might operate critical machinery that cannot support modern authentication protocols. Educational institutions manage thousands of student devices with varying security postures. Hospitality venues must balance guest access convenience with network segmentation requirements.
Common challenges include:
- Device diversity creates authentication complexity across wired, wireless, BYOD, IoT, and legacy systems
- User resistance to complex policies leads to workarounds that undermine security
- Outdated perimeter security models fail to address internal threats and lateral movement
- Legacy and OT devices lack agent support for posture assessment
- Over-engineered policies cause legitimate access failures and helpdesk overload
Understanding these challenges is vital before designing workflows. Traditional network access controller implementations must account for technical limitations whilst maintaining usability. The network access control landscape continues evolving as organisations adopt hybrid work models and cloud services.
Successful policy workflows balance security requirements with operational reality. You cannot simply block all non-compliant devices without understanding business impact. Manufacturing environments often require passive monitoring for OT devices that cannot be interrupted. Educational settings need flexible policies that accommodate diverse student devices whilst protecting sensitive data. Hospitality networks must segment guest traffic without creating friction in the user experience.
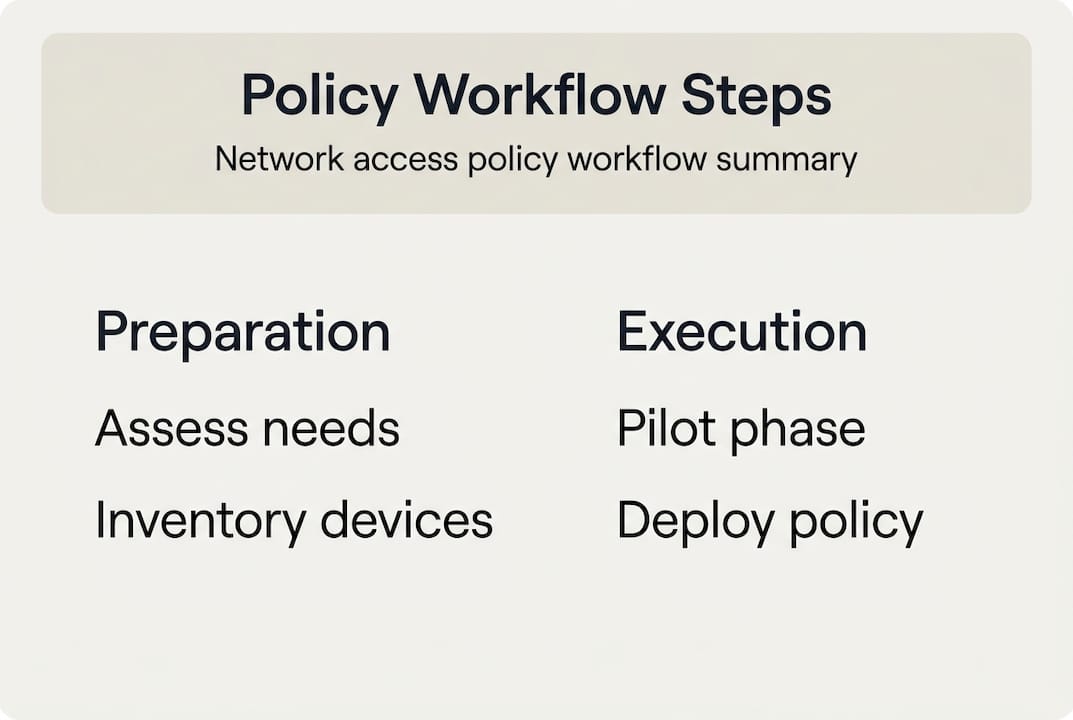
Preparing your network access policy workflow
Preparation determines whether your network access policy workflow succeeds or creates operational chaos. Start by assessing your organisation’s environment, device types, and security posture requirements. Document current network architecture, identify all device categories, and map user groups to access requirements.
Sector-specific considerations shape your approach. Network access policy nuances vary significantly across sectors. Education environments require BYOD focus with flexible authentication for diverse student devices. Manufacturing demands passive OT NAC approaches that monitor without disrupting production systems. Hospitality needs robust guest segmentation and high-density WiFi management.
| Sector | Primary challenge | Recommended approach |
|---|---|---|
| Education | BYOD device diversity and student privacy | Flexible authentication with tiered access based on device compliance |
| Manufacturing | Legacy OT devices without agent support | Passive NAC with network segmentation and anomaly detection |
| Hospitality | Guest access and high-density WiFi | Automated guest provisioning with strict VLAN isolation |
Plan phased deployment to mitigate risk. Pilot programmes allow you to test policies with limited user groups before organisation-wide rollout. Start with a single department or building to identify issues early. Monitor user feedback and access logs to refine policies before expanding scope.

Assess legacy device support needs carefully. Many organisations operate equipment that cannot support 802.1X authentication or endpoint agents. These devices require alternative approaches such as MAC address authentication, passive profiling, or dedicated network segments. Document all legacy systems and plan appropriate accommodation strategies.
Develop clear documentation of requirements and engage stakeholders early. IT security, network operations, and business unit leaders must align on policy objectives and acceptable trade-offs. User education programmes reduce resistance and improve compliance. When comparing Meraki access control vs Cisco ISE, consider your organisation’s technical capabilities and support resources.
Pro Tip: Create a device inventory spreadsheet categorising every device type by authentication capability, business criticality, and security risk. This inventory becomes your roadmap for policy design and helps identify quick wins versus complex edge cases.
Consider sector-specific infrastructure requirements. Manufacturing environments often require OT network segmentation strategies. Hospitality networks demand seamless guest onboarding with robust backend security. Tailoring your preparation to sector realities prevents costly redesigns later.
Executing network access policy workflows step by step
Implementation transforms preparation into operational security. Follow these steps to deploy your network access policy workflow systematically.
-
Define and categorise device and user groups for tailored access control. Create profiles for corporate devices, BYOD, guests, IoT sensors, and legacy systems. Each group receives appropriate authentication requirements and network access privileges.
-
Implement authentication mechanisms matched to device capabilities. Deploy 802.1X for managed corporate devices, MAC authentication bypass for IoT devices, and web portal authentication for guests. Agentless NAC solutions accommodate devices that cannot install endpoint software.
-
Start with monitor-only mode to detect policy issues without blocking users. This approach reveals authentication failures, device profiling gaps, and policy conflicts before enforcement begins. Monitor logs for two to four weeks to establish baseline behaviour.
-
Configure posture assessment for corporate devices. Check for operating system updates, antivirus status, and security configuration before granting network access. Non-compliant devices receive remediation instructions or quarantine VLAN assignment.
-
Address legacy and OT devices using passive NAC approaches and hybrid workflows. Legacy devices that cannot use 802.1X or agents require passive monitoring. Over-complex policies cause user resistance and authentication failures. Monitor-only deployment prevents lockouts. Hybrid pre-admission and post-admission controls balance security with operational continuity.
-
Implement VLAN segmentation and guest networks where applicable. Separate corporate, guest, and IoT traffic using VLANs. Guest networks receive internet-only access without lateral movement capabilities. IoT devices operate in isolated segments with restricted communication paths.
-
Iterate policies and gradually enforce access restrictions. Begin enforcement with low-risk user groups. Expand to additional groups as confidence grows. Maintain helpdesk readiness to address authentication issues quickly.
Pro Tip: Keep policies simple and clear to reduce user friction and drive adoption. Complex multi-factor authentication requirements for low-risk access create workaround behaviours that undermine security. Match authentication strength to data sensitivity and access privilege.
Follow network security best practices throughout implementation. Regular compliance scanning identifies configuration drift and policy violations. Comprehensive network access controller guidance helps navigate technical implementation details.
Document every policy decision and exception. Future administrators need context for understanding why certain devices receive special treatment. Clear documentation prevents security degradation when staff turnover occurs. Include business justification, technical limitations, and compensating controls for each policy exception.
Verifying and maintaining your network access policy workflow
Deployment marks the beginning, not the end, of network access policy management. Ongoing verification and maintenance ensure policies remain effective as your environment evolves.
Test policy workflows in controlled scenarios before full enforcement. Create test accounts representing each user type. Attempt access from compliant and non-compliant devices. Verify that authentication succeeds for authorised users and fails appropriately for policy violations. Document test results and remediate issues before expanding enforcement.
Monitor user experience and access logs continuously. Track authentication success rates, policy violation trends, and helpdesk ticket volumes. Sudden increases in authentication failures indicate policy misconfigurations or environmental changes requiring investigation. User feedback reveals friction points that drive workaround behaviours.
Use phased enforcement to reduce operational disruption. Begin with notification-only mode where policy violations generate alerts without blocking access. Progress to quarantine mode where non-compliant devices receive limited network access. Finally, implement full enforcement mode with access denial for policy violations. Each phase allows tuning before increasing restriction severity.
| Feature | Traditional NAC | Zero Trust Network Access |
|---|---|---|
| Verification timing | Pre-admission only | Continuous post-admission |
| Trust model | Perimeter-based | Never trust, always verify |
| Segmentation | VLAN-based | Microsegmentation |
| Access control | Role-based static policies | Context-aware dynamic policies |
| Legacy device support | Limited agent options | Agentless monitoring |
Zero Trust integration represents the evolution from traditional NAC to ZTNA and microsegmentation for continuous verification and just-in-time access. This contrasts with traditional perimeter models that grant broad access after initial authentication. Modern approaches verify every access request based on current context, device posture, and user behaviour.
Regularly review policies and incorporate microsegmentation principles. Network segmentation limits lateral movement even when attackers compromise individual devices. Just-in-time access controls grant privileges only when needed and revoke them automatically after task completion. These approaches strengthen security posture beyond traditional static policies.
Establish routine audits and compliance scans to maintain security over time. Quarterly policy reviews ensure alignment with current business requirements and threat landscape. Compliance risks and security automation help identify configuration drift and policy violations before they create vulnerabilities.
Key verification activities include:
- Monthly access log reviews to identify anomalous authentication patterns
- Quarterly device inventory audits to discover unauthorised devices
- Semi-annual policy effectiveness assessments measuring security outcomes
- Annual architecture reviews evaluating Zero Trust maturity progression
Consider Cisco Access Manager for Zero Trust implementations that provide continuous verification capabilities. Understanding the crucial role of Zero Trust helps prioritise modernisation efforts. Implement network security best practices throughout the verification lifecycle.
Pro Tip: Create a policy dashboard showing authentication success rates, policy violation trends, and security posture metrics. Visual monitoring helps identify issues quickly and demonstrates security programme value to leadership.
Enhance your network security with expert solutions
Implementing robust network access policies requires specialised expertise and ongoing support. Re-Solution offers tailored IT infrastructure services to help organisations design, deploy, and maintain effective network access policy workflows.
Our network access controller expertise helps you navigate complex implementation challenges across education, manufacturing, and hospitality sectors. We understand the unique requirements of each environment and deliver solutions that balance security with operational efficiency. Comprehensive IT infrastructure guidance ensures your network foundation supports advanced access control capabilities.
Cisco managed IT services provide continuous monitoring and policy enforcement to maintain security posture over time. Our team handles the technical complexity whilst you focus on core business objectives. With over 35 years of experience as a trusted Cisco partner, we deliver proven outcomes for organisations seeking robust connectivity, compliance, and security solutions.
Frequently asked questions
How does network access control improve security?
NAC improves security by verifying device compliance and user identity before granting network access. This prevents unauthorised devices from connecting and limits access based on security posture. Continuous monitoring detects policy violations and anomalous behaviour that indicate potential threats.
What types of devices can NAC manage effectively?
NAC manages wired devices, wireless endpoints, BYOD smartphones, tablets, IoT sensors, and user identities across diverse platforms. Legacy and OT devices that lack modern authentication capabilities require passive NAC approaches with network profiling. Most modern NAC solutions accommodate agentless monitoring for devices that cannot install endpoint software.
What’s the benefit of phased deployment for access policies?
Phased deployment reduces risks of network lockouts and operational disruption during policy rollout. It allows policy tuning based on real-world feedback before full enforcement begins. Starting with monitor-only mode identifies configuration issues without blocking legitimate access. Gradual enforcement builds user confidence and reduces helpdesk burden.
How does Zero Trust Network Access differ from traditional NAC?
Zero Trust continuously verifies users and devices throughout their session using microsegmentation and context-aware policies. Traditional NAC performs verification primarily at network admission and grants broader access afterward. ZTNA assumes breach and limits lateral movement through granular segmentation. This approach provides stronger protection against internal threats and compromised credentials. Learn more about network security best practices for modern implementations.
Recommended
- Network Access Controller Guide | Secure Network | Re-Solution
- Network Security Best Practices Guide | Re-Solution
- Meraki Security, Cisco NGFW
- How to Build a Secure Network: Step-by-Step | Re-Solution
- How to Review Access for Secure Team Collaboration
- Compliance Admin: Streamline Security Questionnaire Workflow